Lab: Exploiting server-side parameter pollution in a query string
Server Side parameter pollution
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/lab-exploiting-server-side-parameter-pollution-in-a … ⌘ Read more
Breaking Twitter’s VPN: $20,160 Bounty for a Pre-Auth RCE via Pulse Secure Chain
How Orange Tsai & Meh Chang Combined File Read, Session Hijack, and Admin Injection to Breach Twitter’s Internal … ⌘ Read more
**One Endpoint to Rule Them All: How I Chained 3 Bugs into Full Account Takeover **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/one-endpoint-to-rule-them-all-h … ⌘ Read more
Demystifying Cookies : The Complete Guide for Bug Bounty Hunters — Part 1
Everything you need to know about cookies to expand your attack surface and find real bugs.
[Continue reading on InfoSec Write-ups »](h … ⌘ Read more
**Silent but Deadly: How Blind XSS in Email Notifications Gave Me Root Alerts **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/silent-but-deadly-how-blind-xss-in-email … ⌘ Read more
DFIR: An Introduction | TryHackMe Write-Up | FarrosFR
Here is my article on the walkthrough of a free room: DFIR: An Introduction. Introductory room for the DFIR module. I wrote this in 2025…
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/ … ⌘ Read more
MITM HTTPS Payload with Python
A lightweight MITM tool for monitoring encrypted traffic and detecting threats powered by AI and built in Python
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/mitm-https-payload-with-python-499ebf8e933f?source=rss—-7b722bfd1b8d— … ⌘ Read more
**From CSP to OMG: How a Tiny Misconfigured Header Let Me Run JS Anywhere **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/from-csp-to-omg-how-a-tiny-misconfigured-header-let- … ⌘ Read more
I Gave Myself 60 Minutes to Find a Bug — This Is What Happened
Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/i-gave-myself-60-minutes-to-find-a-bug-this-is-what-happened-e5fa76563a33?so … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1353 ARCHIVED:87369 CACHE:2680 FOLLOWERS:22 FOLLOWING:14
Maybe you’ll enjoy this as well:
I still have one of my first modems, a Creatix LC 144 VF:

I think this was the modem that I used when I first connected to the internet, but I’m not sure.
I plugged it in again and it still works:
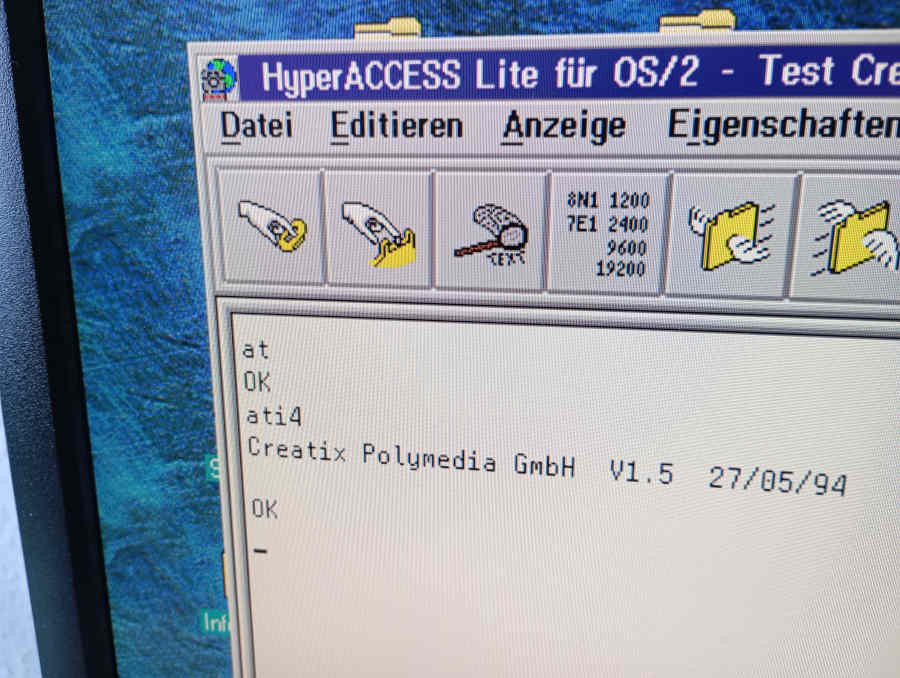
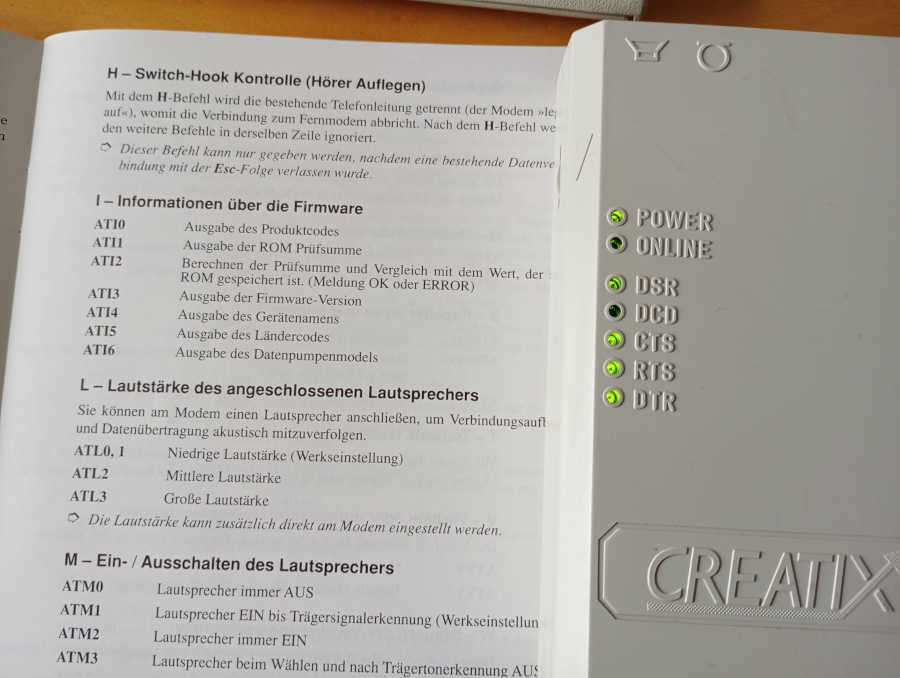
The firmware appears to be from 1994, which sounds about right. I don’t think we had internet access before that. We certainly did use local mailboxes, though. (Or BBS’s, as you might call them.)
I now want to actually use that modem again. For the moment, I can only use a phone to dial into it, I lack a second modem to actually establish a connection. Here’s a video:
Not spectacular, but the modem does answer after me entering ATA.
I bought another cheap old modem on eBay and am now waiting for it to arrive. Once it’s here, I want to simulate an actual dial-up session, hopefully from OS/2 or Windows 3.x.
Trump crashes Russian stock market: minus US$1 billion in few hours ⌘ Read more
Drones hit Russia’s Shahed drone factory 1,200 km from Ukraine again ⌘ Read more
From Zero to $1000/Month | Bug Bounty Automation Blueprint
Proven Tactics, Tools, and Code to Automate Your Way to Consistent Bounties
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/from-zero-to-1000-month-bug-boun … ⌘ Read more
️My Top 7 Mistakes as a New Bug Hunter (And How to Avoid Them)
Free Article Link only for you
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/%EF%B8%8Fmy-top-7-mistakes-as-a-new-bug-hunter- … ⌘ Read more
** The Misconfigured Magnet: How Public Buckets Exposed Millions of User Files **
Hey there😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/the-misconfigured-magnet-how-public-buck … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1352 ARCHIVED:87359 CACHE:2686 FOLLOWERS:22 FOLLOWING:14
UE1 homebrew 1-bit vacuum computer in action
full series playlist
🧮 USERS:1 FEEDS:2 TWTS:1351 ARCHIVED:87339 CACHE:2704 FOLLOWERS:22 FOLLOWING:14
One of the nicest things about Go is the language itself, comparing Go to other popular languages in terms of the complexity to learn to be proficient in:
- Go:
25keywords (Stack Overflow); CSP-style concurrency (goroutines & channels)
- Python 2:
30keywords (TutorialsPoint); GIL-bound threads & multiprocessing (Wikipedia)
- Python 3:
35keywords (Initial Commit); GIL-bound threads,asyncio& multiprocessing (Wikipedia, DEV Community)
- Java:
50keywords (Stack Overflow); threads +java.util.concurrent(Wikipedia)
- C++:
82keywords (Stack Overflow);std::thread, atomics & futures (en.cppreference.com)
- JavaScript:
38keywords (Stack Overflow); single-threaded event loop &async/await, Web Workers (Wikipedia)
- Ruby:
42keywords (Stack Overflow); GIL-bound threads (MRI), fibers & processes (Wikipedia)
@movq@www.uninformativ.de i feel like when i read go code i’m reading some algebra shit where every part is 1-5 letters long and then there’s weird symbols like := and it’s just infinitely harder for me to parse and infer meaning from lol. it’s such a me problem
More than 1,900 Americans applied for UK citizenship as Trump began second term ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1350 ARCHIVED:87332 CACHE:2725 FOLLOWERS:22 FOLLOWING:14
U.S. reports cases of new COVID variant NB.1.8.1 behind surge in China ⌘ Read more
This is one of my attempts: 
$ go build ./cmd/xor/... && ./xor
Generation 95 | Fitness: 0.999964 | Nodes: 9 | Conns: 19
Target reached!
Best network performance:
[0 0] → got=0 exp=0 (raw=0.000) ✅
[0 1] → got=1 exp=1 (raw=0.990) ✅
[1 0] → got=1 exp=1 (raw=0.716) ✅
[1 1] → got=0 exp=0 (raw=0.045) ✅
Overall accuracy: 100.0%
Wrote best.dot – render with `dot -Tpng best.dot -o best.png`
Trump recommends 50% tariff on European Union starting June 1 ⌘ Read more
fit 1 $ spin (saw 0.1 * sign fxy) $ rect 0 1 - rect 0 0.99 >> add;#punctual #livecoding #creativecoding #videoart
🧮 USERS:1 FEEDS:2 TWTS:1349 ARCHIVED:87324 CACHE:2738 FOLLOWERS:22 FOLLOWING:14
Adafruit Hit With $36K Tariff Bill on 1,000 lbs of Electronics
Adafruit CEO responds to The Lunduke Journal with details and stays non-political about changing tariffs. ⌘ Read more
6.1.140: longterm
Version:6.1.140 (longterm)Released:2025-05-22Source:linux-6.1.140.tar.xzPGP Signature:linux-6.1.140.tar.signPatch:full ( incremental)ChangeLog:ChangeLog-6.1.140 ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1348 ARCHIVED:87166 CACHE:2773 FOLLOWERS:22 FOLLOWING:14
** They Missed This One Tiny Parameter — I Made $500 Instantly**
✨Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/they-missed-this-one-tiny-parameter-i-made-500-instantly-f2f7d1c1c1d9?source=rss—-7 … ⌘ Read more
The Battle for Python’s Soul: How uv is Challenging pip’s Championship Reign
The stadium lights flicker on. The crowd falls silent. In the blue corner, weighing in with over a decade of dominance and … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1347 ARCHIVED:87160 CACHE:2773 FOLLOWERS:22 FOLLOWING:14
$1 Million Tax Payer Grant for “Gender Inclusive Open Source”
A cancelled grant, worth a million bucks, for Oregon State University to create “best practices for fixing gender-bias bugs”. ⌘ Read more
Rabbit Store | TryHackMe Medium
Problems: What is user.txt? What is root.txt? Solution: First of all we get a IP address so I preformed an NMAP scan discovering ports…
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/rabbit-store-tryhackme-medium-f9f5069fbb50?source=r … ⌘ Read more
Mastering SQL Injection Recon: Step-by-Step Guide for Bug Bounty Hunters
A practical guide to uncovering SQL injection flaws using automation, payloads and deep reconnaissance techniques.
[Continue reading … ⌘ Read more
Build Your Own AI SOC — Part 7 Build a Security Knowledge Assistant With RAG + GPT
From Search to Understanding
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/build-you … ⌘ Read more
Exciting Cybersecurity Careers That Don’t Require Coding
Do you believe that cybersecurity is only for programmers who are bent over keyboards, typing code after code to ward off hackers? Rethink…
[Continue reading on InfoSec Write-ups »] … ⌘ Read more
Writing Pentest Reports | TryHackMe Write-Up | FarrosFR
Non-members are welcome to access the full story here. Write-Up by FarrosFR | Cybersecurity
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/writing-pentest-reports-tryhackme-wri … ⌘ Read more
