**WooCommerce Users Beware: Fake Patch Phishing Campaign Unleashes Site Backdoors **
Imagine this: you’re running your WooCommerce store, sipping coffee ☕, and an urgent email lands in your inbox. It scr … ⌘ Read more
** JWT, Meet Me Outside: How I Decoded, Re-Signed, and Owned the App **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/jwt-meet-me-outside-how-i-decoded-re-signed-and-owned-the-app-95791eabcf5d? … ⌘ Read more
**Hackers Exploit Craft CMS Flaws: A Deep Dive into CVE-2025–32432 **
Imagine running a sleek website powered by Craft CMS, only to discover that hackers have slipped through the digital backdoor, wreaking…
[Continue reading on Info … ⌘ Read more
$300 Google Cloud Free Trial: Create Your First VM
Non-members can read this article for free using this link.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/300-google-cloud-free-trial-create-your-first-vm-5a12b6821b0f?source=r … ⌘ Read more
**Master Spring Boot APIs Like a Pro: Skills That Distinguish Good Developers from Great Ones **
In the fast-moving world of backend development, it’s no longer enough to … ⌘ Read more
Mastering Java Records: The Ultimate Guide to Cleaner, Faster, and Immutable Code
Introduction
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/mastering-java-records-the … ⌘ Read more
** Microsoft Fortifies MSA Signing Infrastructure with Azure Confidential VMs After Storm-0558…**
In the ever-evolving cyber threat landscape, 2023 saw one of the most talked-ab … ⌘ Read more
** CloudImposer: How a Malicious PyPI Package Could’ve Hijacked Google Cloud Composer**
In early 2025, a critical vulnerability in Google Cloud Platform’s (GCP) Cloud Composer service came to light, … ⌘ Read more
**DslogdRAT Malware: A Sneaky Cyberattack Exploiting Ivanti ICS Zero-Day **
Buckle up, cybersecurity enthusiasts! 🚀 A new villain has entered the digital stage: DslogdRAT, a stealthy malware that’s been causing…
[Continue r … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1325 ARCHIVED:86778 CACHE:2902 FOLLOWERS:22 FOLLOWING:14
Trinity Desktop Environment R14.1.4 released
The Trinity Desktop Environment, the modern-day continuation of the KDE 3.x series, has released version R14.1.4. This maintenance release brings new vector wallpapers and colour schemes, support for Unicode surrogate characters and planes above zero (for emoji, among other things), tabs in kpdf, transparency and other new visual effects for Dekorator, and much more. TDE R14.1.4 is already available for a variety of Linux distributions, and c … ⌘ Read more
☁️How to Setup a Custom Subdomain on xss.ht — A Complete Hacker’s Guide
Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/%EF%B8%8Fhow-to-setup-a-custom-subdom … ⌘ Read more
$500 Bounty: For a Simple Open Redirect
How a Language Chooser Flaw Led to Open Redirect and Server Issues on HackerOne
** Login? Who Needs That? Bypassing OAuth Like a Lazy Hacker on Sunday ☀️**
Free Link🎈
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/login-who-needs-that-bypassing-oauth-like-a- … ⌘ Read more
** How to Turn Cybersecurity Into a Full-Time Income (My Blueprint)**
💡Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/how-to-turn-cybersecurity-into-a-full-time-income-my-blueprint-f4d70 … ⌘ Read more
** Rack::Static Vulnerability Exposes Ruby Servers to Data Breaches! **
Hold onto your keyboards, Ruby developers! 😱 A critical security flaw in the Rack::Static middleware has been uncovered, potentially…
[Continue reading on InfoS … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1324 ARCHIVED:86731 CACHE:2910 FOLLOWERS:22 FOLLOWING:14
AnalogLamb Expands Maple Series with Low-Cost ESP32C6 Breakout Boards
AnalogLamb has introduced three new RISC-V development boards based on the ESP32-C6, designed for low-cost, full-function, and low-power IoT applications. These boards feature Espressif’s first Wi-Fi 6 SoC, integrating Wi-Fi 6 (2.4 GHz), Bluetooth 5 LE, and IEEE 802.15.4 protocols. Each board is built around the ESP32-C6-WROOM-1 module, which combines a high-performance 32-bit RISC-V core […] ⌘ Read more
Can you automate the drawing with a script? On X11, you can:
#!/bin/sh
# Position the pointer at the center of the dot, then run this script.
sleep 1
start=$(xdotool getmouselocation --shell)
eval $start
r=400
steps=100
down=0
for step in $(seq $((steps + 1)) )
do
# pi = 4 * atan(1)
new_x=$(printf '%s + %s * c(%s / %s * 2 * (4 * a(1)))\n' $X $r $step $steps | bc -l)
new_y=$(printf '%s + %s * s(%s / %s * 2 * (4 * a(1)))\n' $Y $r $step $steps | bc -l)
xte "mousemove ${new_x%%.*} ${new_y%%.*}"
if ! (( down ))
then
xte 'mousedown 1'
down=1
fi
done
xte 'mouseup 1'
xte "mousemove $X $Y"

Interestingly, you can abuse the scoring system (not manually, only with a script). Since the mouse jumps to the locations along the circle, you can just use very few steps and still get a great score because every step you make is very accurate – but the result looks funny:
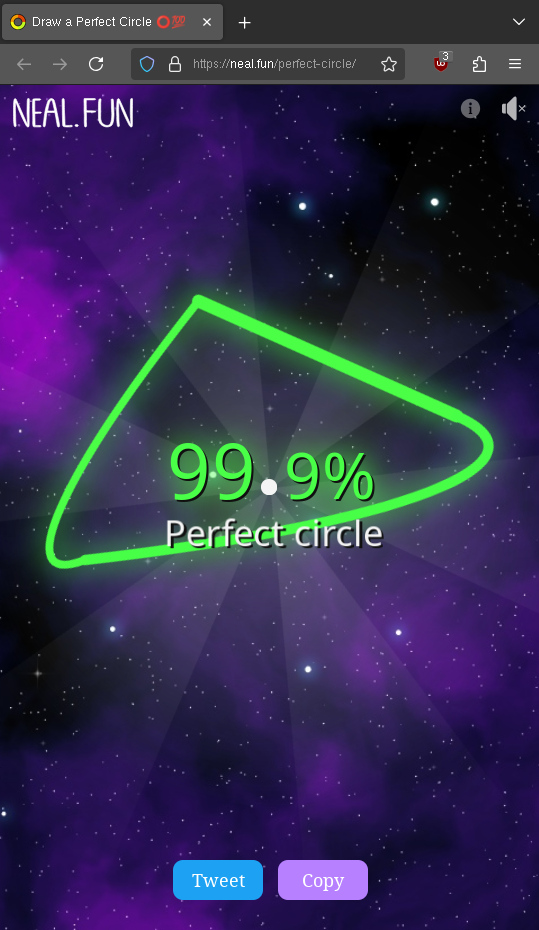
🥴
🧮 USERS:1 FEEDS:2 TWTS:1323 ARCHIVED:86698 CACHE:2903 FOLLOWERS:22 FOLLOWING:14
How We Diagnosed and Fixed the 2023 Voyager 1 Anomaly from 15 Billion Miles Away
Comments ⌘ Read more
On my blog: Free Culture Book Club — Pilogy, part 1 https://john.colagioia.net/blog/2025/04/26/pilogy-1.html #freeculture #bookclub
⏱️ There were no visible errors, no hints… only the server’s hesitation told me the truth.
It didn’t scream. It whispered… and I heard it.
[Continue reading on I … ⌘ Read more
**Path Traversal Attack: How I Accessed Admin Secrets **
Path Traversal Attack: How I Accessed Admin Secrets 📂
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/path-traversal-attack-how-i-accessed-admin-secrets-fa5de1865031?source … ⌘ Read more
Top 5 Open Source Tools to Scan Your Code for Vulnerabilities
These tools help you find security flaws in your code before attackers do.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/top-5-open-source-tools-to-s … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1321 ARCHIVED:86594 CACHE:2833 FOLLOWERS:21 FOLLOWING:14
Building trust with OpenID Federation trust chain on Keycloak
OpenID Federation 1.0 provides a framework to build trust between a Relying Party and an OpenID Provider that have no direct relationship so that the Relying Party can send OIDC/OAuth requests to the OpenID Provider without being previously… ⌘ Read more
LitmusChaos at KubeCon + CloudNativeCon Europe 2025: A Recap
The cloud native community recently converged in London from April 1 – 4, 2025, for an incredible edition of KubeCon + CloudNativeCon Europe. From our perspective at LitmusChaos, it was a week filled with inspiring sessions,… ⌘ Read more
6.1.135: longterm
Version:6.1.135 (longterm)Released:2025-04-25Source:linux-6.1.135.tar.xzPGP Signature:linux-6.1.135.tar.signPatch:full ( incremental)ChangeLog:ChangeLog-6.1.135 ⌘ Read more
**The Fastest Way to Learn Web Hacking in 2025 (With Free Resources) **
🔓Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/the-fastest-way-to-learn-web-hacking-in-2025-with-free-resourc … ⌘ Read more
Hidden Tricks to Spot Phishing Emails Before They Trick You!
Phishing emails are like traps set by cybercriminals to trick you into sharing personal details, clicking dangerous links, or downloading…
[Continue reading on InfoSec Write-ups … ⌘ Read more
** Hostile Host Headers: How I Hijacked the App with One Sneaky Header **
Hey there!😊
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/hostile-host-headers-how-i-hijacked-the-app-with-one-sneaky-hea … ⌘ Read more
GitLab CI for Python Developers: A Complete Guide
Automating Testing, Linting, and Deployment for Python projects using GitLab CI/CD
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/gitlab-ci-for-python-developers-a-complete-guide-83794cb91 … ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1320 ARCHIVED:86540 CACHE:2803 FOLLOWERS:21 FOLLOWING:14
** How I discovered a hidden user thanks to server responses ?**
My first real step into web hacking and it wasn’t what i thought it would be.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/how-i-discovered-a-hidde … ⌘ Read more
How to Build a Threat Detection Pipeline from Scratch (Like a Cyber Ninja!)
Hey, cyber fam! Have you ever asked yourself:
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/how-to-build-a-threat … ⌘ Read more
Nothing changed… except for one detail. And that was enough to hack
Sometimes, hacking doesn’t require any exploit… just good observation.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/nothing-c … ⌘ Read more
How to Create a Botnet Using One Tool: A Proof of Concept for Educational Purposes Aspiring…
Learn how attackers build and control botnets — safely and ethically — using … ⌘ Read more
**Burp, Bounce, and Break: How Web Cache Poisoning Let Me Control the App **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/burp-bounce-and-break-how-web-cache-poisoning-let-me-con … ⌘ Read more
OWASP Juice Shop | Part 1 — ScoreBoard Solution — StrawHat Hackers ⌘ Read more
🧮 USERS:1 FEEDS:2 TWTS:1319 ARCHIVED:86501 CACHE:2810 FOLLOWERS:21 FOLLOWING:14
I Lost $3,750 in 30 Seconds — The ATO Bug 99% of Hackers Miss (Here’s How to Avoid It)
The 1 Burp Suite Mistake That Cost Me $3,750 — Fix It in 30 Seconds
[Continue reading on InfoSec Writ … ⌘ Read more
SOC L1 Alert Reporting : Step-by-Step Walkthrough | Tryhackme
As a SOC analyst, it is important to detect high-severity logs and handle them to protect against disasters. A SOC analyst plays the…
[Continue reading on InfoSec Write-ups … ⌘ Read more
**404 to 0wnage: How a Broken Link Led Me to Admin Panel Access **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/404-to-0wnage-how-a-broken-link-led-me-to-admin-panel-access-2b58e1fffaa3?source=r … ⌘ Read more
How to Start Bug Bounty in 2025 (No Experience, No Problem)
✅Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/how-to-start-bug-bounty-in-2025-no-experience-no-problem-89adc68da592?source=rss—-7b … ⌘ Read more