As we reach mid-year 2024, a look at CNCF, Linux Foundation, and top 30 open source project velocity
Staff post by Chris Aniszczyk Date/Time: July 11 at 8am For the last several years we have tracked open source project velocity, which has enabled us to monitor the trends and technologies that resonate with developers and end… ⌘ Read more
What is retrieval-augmented generation, and what does it do for generative AI?
Here’s how retrieval-augmented generation, or RAG, uses a variety of data sources to keep AI models fresh with up-to-date information and organizational knowledge.
The post What is retrieval-augmented generation, and what does it do for generative AI? appeared first on [T … ⌘ Read more
Hi @movq@www.uninformativ.de, is it better now?
I have put in a psudo twthash since I did not archive from a specific date/post, but just what I did not find relevant to keep in my main feed.
How to Hide the Clock at MacOS Login Screen
The Mac login screen and lock screen displays a prominent large clock, with the date and time visible over the wallpaper or screensaver. While many users appreciate having the time and date right there at the login screen, other users may wish to hide the clock, date, and time, from the MacOS login screen. If … Read More ⌘ Read more
Apple Cancels the Apple Car Project
Apple has canceled their ambitious decade-long car project, codenamed Project Titan, according to a report from Bloomberg. Development on the Apple Car, which was apparently intended to be an electric vehicle with self-driving capabilities, became news in 2015, and originally had a speculative release dates of 2019 and 2020, which obviously came and went without … Read More ⌘ Read more
‘A lot of contentious issues on the agenda’: Australia and China preparing for high-level talks
Details and dates are still to be determined and announced, but experts say a range of thorny issues could be on the table. ⌘ Read more
GitHub Copilot Enterprise is now generally available
Our most advanced AI offering to date is customized to your organization’s knowledge and codebase, infusing GitHub Copilot throughout the software development lifecycle.
The post GitHub Copilot Enterprise is now generally available appeared first on The GitHub Blog. ⌘ Read more
Sad to see moc removed from the official arch linux repos, but also cool to learn the debian project has been quietly patching it and keeping it up to date in recent years. Long live the music on console player. (And debian!) :-)
“You know who makes very good sandwiches? Felix! Did you ever taste his cream cheese and pimento on date-nut bread?” #nowplaying
Add Corporate Earnings Reports to Your Calendar on Mac, iPhone, iPad via Stocks App
The Stocks app for iPhone, Mac, and iPad, now offers a super convenient way of knowing when a companies upcoming earnings reports will be, and, even better for you earnings season enthusiasts, you can add those earnings report dates directly to your calendar immediately from the Stocks app. Because who doesn’t love listening in on … [Read More](https://osxdaily.com/2024 … ⌘ Read more
Do you know if all your repositories have up-to-date dependencies?
Consider deploying the GitHub Action: Evergreen so that you know each of your repositories are leveraging active dependency management with Dependabot.
The post Do you know if all your repositories have up-to-date dependencies? appeared first on The GitHub Blog. ⌘ Read more
Anyone else noticed how the current date and the climate are more resembling Blade Runner each year.
XMPP Providers: XMPP Providers Fully Automated
Automate all the ThingsDuring the past year, the team behind the XMPP Providers project worked on automating the process of gathering data about XMPP providers.
Automating this process reduces manual work significantly (for example, checking websites by hand, verifying information, listing sources, etc.) and helps to sustain the team’s efforts.
Automation also enables the project to be up to date – every day!
[ … ⌘ Read more
@movq@www.uninformativ.de
Yes I have threading on. I wanted to put new posts at the top with set sort_aux = reverse-last-date-sent but that that makes the threads do the newest first not bellow the reply. So all replies are in a top newest order. But I can just use sort date_sent and then go to the end to go to the newest post.
Should we remove best-before dates on produce?
Advocates say a simple change would stop Australian households from unwittingly throwing out perfectly edible food, and they are banding together to get the regulator on board. ⌘ Read more
How to Use & Access GPT-4 for Free
You may already be using ChatGPT, the phenomenally powerful and useful AI tool, but the free version is based on GPT-3.5. GPT-4 is said to be ten times more advanced, with enhanced creativity, reliability, up-to-date information, and an ability to interpret more nuanced instructions, so it’s understandable why users would like to explore and experience … Read More ⌘ Read more
How to Use & Access GPT-4 for Free
You may already be using ChatGPT, the phenomenally powerful and useful AI tool, but the free version is based on GPT-3.5. GPT-4 is said to be ten times more advanced, with enhanced creativity, reliability, up-to-date information, and an ability to interpret more nuanced instructions, so it’s understandable why users would like to explore and experience … Read More ⌘ Read more
@eapl.me@eapl.me are ISPs still injecting code into HTTP in this the year 2023? I remember getting notices that my comcast modem is out of date pushed into websites back a decade ago.
Date Line
 ⌘ Read more
⌘ Read more
Date Line
 ⌘ Read more
⌘ Read more
@abucci@anthony.buc.ci my last experience with it was with a Debian package which is known for being out of date :-D
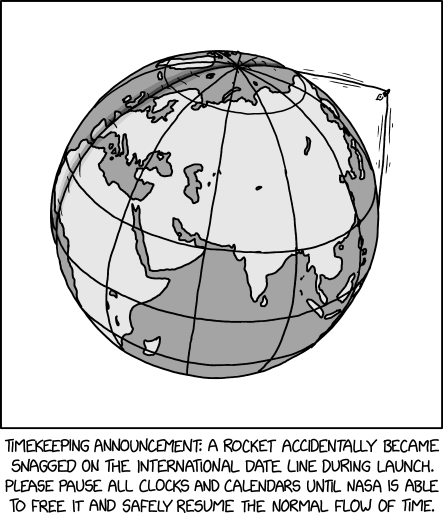
An official FBI document dated January 2021, obtained by the American association “Property of People” through the Freedom of Information Act.
This document summarizes the possibilities for legal access to data from nine instant messaging services: iMessage, Line, Signal, Telegram, Threema, Viber, WeChat, WhatsApp and Wickr. For each software, different judicial methods are explored, such as subpoena, search warrant, active collection of communications metadata (“Pen Register”) or connection data retention law (“18 USC§2703”). Here, in essence, is the information the FBI says it can retrieve:
Apple iMessage: basic subscriber data; in the case of an iPhone user, investigators may be able to get their hands on message content if the user uses iCloud to synchronize iMessage messages or to back up data on their phone.
Line: account data (image, username, e-mail address, phone number, Line ID, creation date, usage data, etc.); if the user has not activated end-to-end encryption, investigators can retrieve the texts of exchanges over a seven-day period, but not other data (audio, video, images, location).
Signal: date and time of account creation and date of last connection.
Telegram: IP address and phone number for investigations into confirmed terrorists, otherwise nothing.
Threema: cryptographic fingerprint of phone number and e-mail address, push service tokens if used, public key, account creation date, last connection date.
Viber: account data and IP address used to create the account; investigators can also access message history (date, time, source, destination).
WeChat: basic data such as name, phone number, e-mail and IP address, but only for non-Chinese users.
WhatsApp: the targeted person’s basic data, address book and contacts who have the targeted person in their address book; it is possible to collect message metadata in real time (“Pen Register”); message content can be retrieved via iCloud backups.
Wickr: Date and time of account creation, types of terminal on which the application is installed, date of last connection, number of messages exchanged, external identifiers associated with the account (e-mail addresses, telephone numbers), avatar image, data linked to adding or deleting.
TL;DR Signal is the messaging system that provides the least information to investigators.
** summer’s lease hath all too short a date **
After the excitement of last summer I was hopeful for a chill one this year. So far, so good.
We visited the island where we used to live and started our family. We saw a few friends, and visited some fa … ⌘ Read more
Announcing the Stale Repos Action
A tool to help you keep your open source catalog organized and up to date. ⌘ Read more
RT by @mind_booster: #COREPERII | The EU Ambassadors just approved setting 6 to 9 June 2024 as the dates for the next European Parliament elections.
#COREPERII | The EU Ambassadors just approved setting 6 to 9 June 2024 as the dates for the next European Parliament elections. ⌘ Read more
Let’s assume for a moment that an answer to a question would be met with so many words you don’t know what the answer was at all. Why? Why do this? Is this a stereotype of academics and philosophers? If so, it’s not a very straight-forward way of thinking, let alone answering a simple question.
Well, I can’t know what’s in these peoples’ minds and hearts. Personally I think it’s a way of dissembling, of sowing doubt, and of maintaining plausible deniability. The strategy is to persuade as many people as possible to change their minds, and then force the remaining people to accept the idea because they think too many other people believe it.
Let’s say you want, for whatever reason, to get a lot of people to accept an idea that you know most people find horrible. The last thing you should do is express the idea clearly and concisely and repeat it over and over again. All you’d accomplish is to cement people’s resistance to you, and label yourself as a person who harbors horrible ideas that they don’t like. So you can’t do that.
What do you do instead? The entire field of “rhetoric”, dating back at least to Plato and Aristotle (400 years BC), is all about this. How to persuade people to accept your idea, even when they resist it. There are way too many techniques to summarize in a twt, but it seems almost obvious that you have to use more words and to use misleading or at least embellished or warped descriptions of things, because that’s the opposite of clearly and concisely expressing yourself, which would directly lead to people rejecting your idea.
That’s how I think of it anyway.
Announcing dates for “Linux Sucks 2023”, “macOS Sucks”, & other events
There’s a lot coming in the weeks ahead! ⌘ Read more
**RT by @mind_booster: Save the date! Feb 13th.
Upcoming webinar: Flexible exceptions - the next step for Europe?
Focus:Open norms and civil law jurisdictions in Europe + a look at the experience of civil law countries in E Asia who have introduced them.
Chair @Senficon
👇🏻
https://www.knowledgerights21.org/news-story/upcoming-webinar-13-february-flexible-copyright-exceptions-the-next-step-for-europe/**
Save the date! Feb 13th.
Upcoming webinar: Flexible exceptions - the next step for Europe?
Focus:Ope … ⌘ Read more
google maps as a dating app
I need to learn how to crash dates that are going nowhere with way too much escalation. That should be fun
[Perl] Date::Holidays::TW 模組的製作與維護 ⌘ Read more
Bad Date
 ⌘ Read more
⌘ Read more
Bad Date
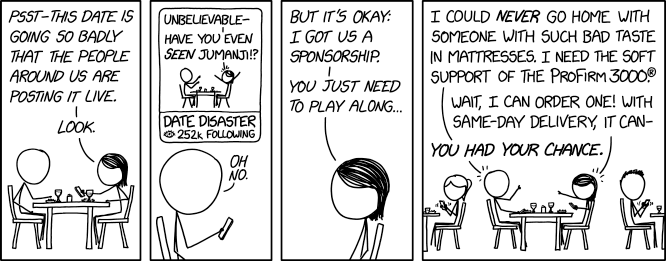 ⌘ Read more
⌘ Read more
Build a game this November with Game Off 2022
Save the date! Game Off returns on November 1 for it’s 10th year! 🎉 ⌘ Read more
Build a game this November with Game Off 2022
Save the date! Game Off returns on November 1 for it’s 10th year! 🎉 ⌘ Read more
asbjorn: “Jeg har snart haft en Toki Pon…”
Jeg har snart haft en Toki Pona-hilsen på min tinder profil i over et år.
Stadig ingen tokiponister der vil samtale.
Har heller ikke været på nogle dates… er der måske en sammenhæng? ⌘ Read more
On the go with GitHub Projects on GitHub Mobile (public beta)
Stay connected and up to date on your work with GitHub Projects on GitHub Mobile, now in public beta. ⌘ Read more
Easy Or Hard
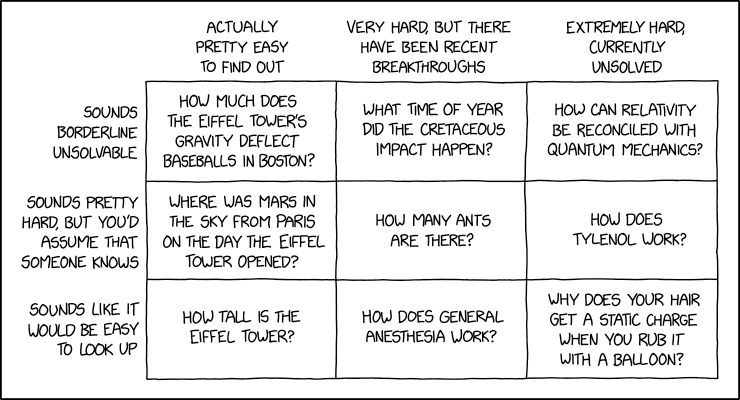 ⌘ Read more
⌘ Read more
Easy Or Hard
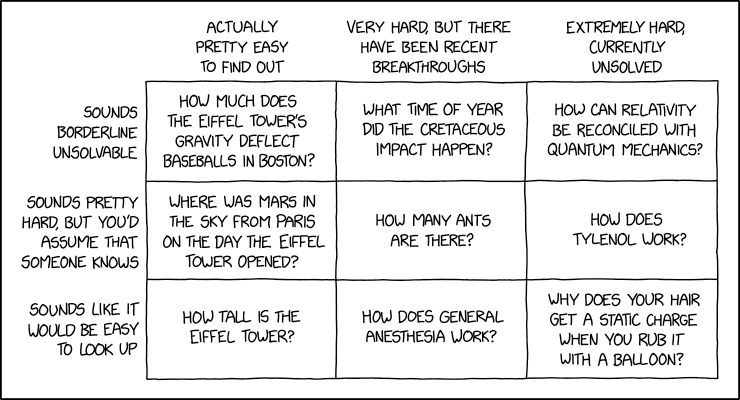 ⌘ Read more
⌘ Read more
Added a section to my XSLT stylesheet explaining what Atom is. That was the point of making it, but I got carried away with date conversion.
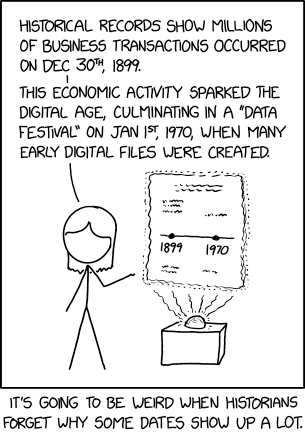
Historical Dates
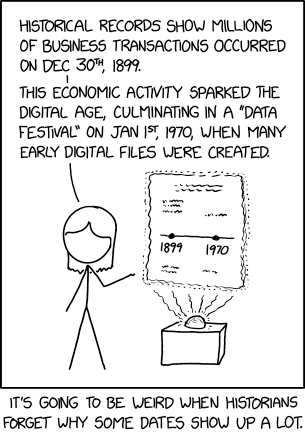 ⌘ Read more
⌘ Read more
Historical Dates
 ⌘ Read more
⌘ Read more
https://twtxt.readthedocs.io/en/latest/user/twtxtfile.html#format-specification fix date format on this twtxt file
JMP: Signup with Cheogram Android
Welcome to JMP.chat! If you are looking for a simple guide on how to sign up for JMP, then you have come to the right place! We will be keeping this guide up-to-date if there is ever a change in how to sign up.
We will first start with signing up from within your Jabber chat application on mobile, where you will never need to leave the client to get set up. I will be using the freedomware Android client Cheogram to do this signup. To star … ⌘ Read more
JMP: Signup with Cheogram Android
Welcome to JMP.chat! If you are looking for a simple guide on how to sign up for JMP, then you have come to the right place! We will be keeping this guide up-to-date if there is ever a change in how to sign up.
We will first start with signing up from within your Jabber chat application on mobile, where you will never need to leave the client to get set up. I will be using the freedomware Android client Cheogram to do this signup. To star … ⌘ Read more
JMP: Signup with Cheogram Android
Welcome to JMP.chat! If you are looking for a simple guide on how to sign up for JMP, then you have come to the right place! We will be keeping this guide up-to-date if there is ever a change in how to sign up.
We will first start with signing up from within your Jabber chat application on mobile, where you will never need to leave the client to get set up. I will be using the freedomware Android client Cheogram to do this signup. To star … ⌘ Read more
Dependabot now alerts for vulnerable GitHub Actions
GitHub Actions gives teams access to powerful, native CI/CD capabilities right next to their code hosted in GitHub. Starting today, GitHub will send a Dependabot alert for vulnerable GitHub Actions, making it even easier to stay up to date and fix security vulnerabilities in your actions workflows. ⌘ Read more
“to limit that rise to 1.5C […] global carbon emissions will have to be reduced by 45% by 2030.
[…]
Instead, we are on course for close to a 14% rise in emissions by that date – which will almost certainly see us shatter the 1.5C guardrail in less than a decade.”
“to limit that rise to 1.5C […] global carbon emissions will have to be reduced by 45% by 2030.
[…]
Instead, we are on course for close to a 14% rise in emissions by that date – which will almost certainly see us shatter the 1.5C guardrai … ⌘ Read more
Hong Kong customs seizes 3.8 tonnes of date rape drug GBL in first half of 2022, dwarfing amount detected over past decade
Despite significant rise in seizures, Customs and Excise Department says Hong Kong has not become a transit hub for illegal drugs. ⌘ Read more