$540 Bounty: How a Misconfigured Warning Endpoint in Apache Airflow Exposed DAG Secrets
CVE-2023–42780: An Improper Access Control Bug That Let Low-Privileged Users View DAG Impo … ⌘ Read more
Banana Pi Previews BPI-R4 Pro Router Board with MediaTek MT7988A and Wi-Fi 7 Support
Banana Pi has revealed early details about the BPI-R4 Pro, an upcoming router board powered by the MediaTek MT7988A (Filogic 880). Designed as a successor to the BPI-R4, it targets high-speed wireless and wired networking for applications such as Wi-Fi 7 access points and multi-gigabit gateways. The BPI-R4 Pro features a quad-core Arm Cortex-A73 CPU […] ⌘ Read more
Memory Analysis Introduction | TryHackMe Write-Up | FarrosFR
Non-members are welcome to access the full story here.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/memory-analysis-introduction-tryhackme-write-up-farrosfr-32e … ⌘ Read more
Logic Flaw: Deleting HackerOne Team Reports Without Access Rights
How a GraphQL Mutation Allowed Unauthorized Report Deletion Across Teams
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/logic-flaw … ⌘ Read more
This One Hacker Trick Got Me Access to an Admin Dashboard ️
Sometimes, it’s not about brute force. It’s about finesse. One header. One oversight. One open door.
— A Hacker’s Mindset 🧠
[Continue reading on InfoSec … ⌘ Read more
$500 Bounty: Shopify Referrer Leak: Hijacking Storefront Access with a Single Token
Referrer Header Leaks + Iframe Injection = Storefront Password Bypass
[Continue reading on InfoSec Writ … ⌘ Read more
Hacking Insights: Gaining Access to University of Hyderabad Ganglia Dashboard ⌘ Read more
Maybe you’ll enjoy this as well:
I still have one of my first modems, a Creatix LC 144 VF:

I think this was the modem that I used when I first connected to the internet, but I’m not sure.
I plugged it in again and it still works:
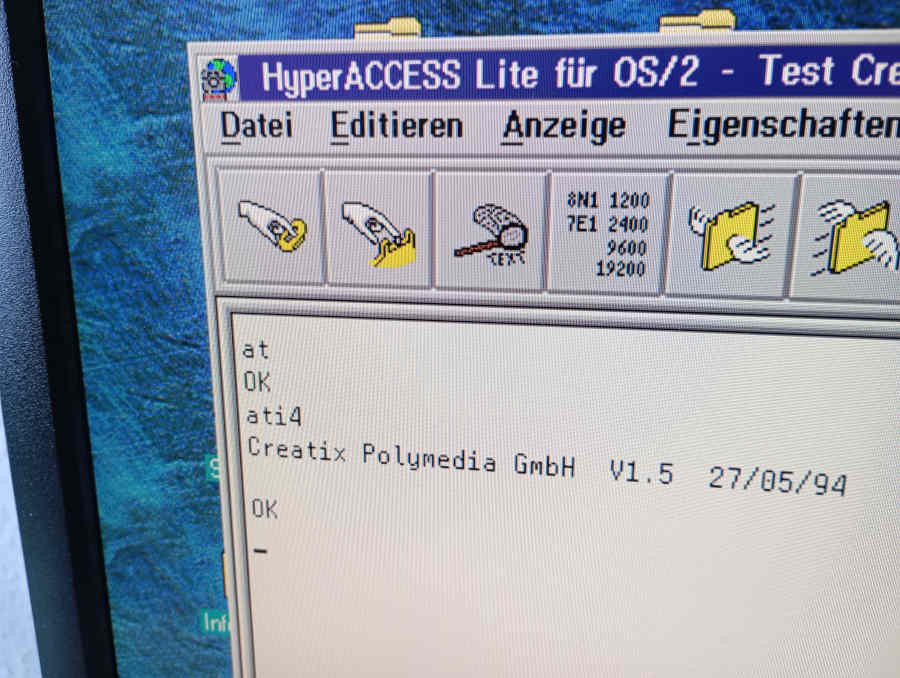
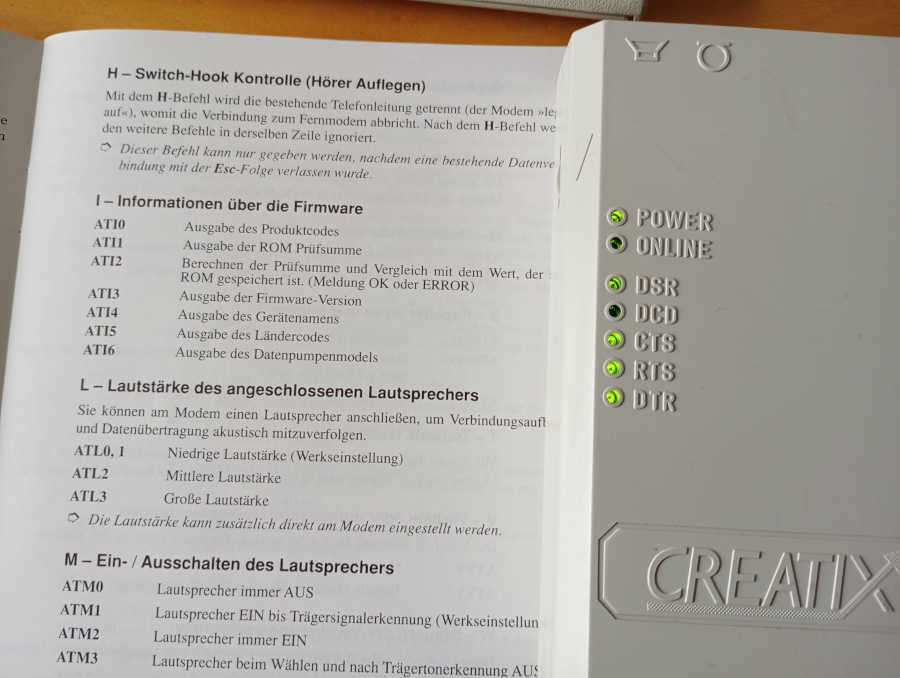
The firmware appears to be from 1994, which sounds about right. I don’t think we had internet access before that. We certainly did use local mailboxes, though. (Or BBS’s, as you might call them.)
I now want to actually use that modem again. For the moment, I can only use a phone to dial into it, I lack a second modem to actually establish a connection. Here’s a video:
Not spectacular, but the modem does answer after me entering ATA.
I bought another cheap old modem on eBay and am now waiting for it to arrive. Once it’s here, I want to simulate an actual dial-up session, hopefully from OS/2 or Windows 3.x.
NanoKVM Pro Delivers 4K IP-KVM Capabilities with Dual-System Support and Enhanced Remote Management
The NanoKVM Pro is a compact IP-KVM device designed for remote access, system control, and local display monitoring. Building on the earlier NanoKVM, this version introduces 4K resolution support, improved connectivity, and broader compatibility with open-source platforms. This device enables real-time remote desktop access at up to 4K at 30 fram … ⌘ Read more
GhostBSD: from usability to struggle and renewal
This article isn’t meant to be technical. Instead, it offers a high-level view of what happened through the years with GhostBSD, where the project stands today, and where we want to take it next. As you may know, GhostBSD is a user-friendly desktop BSD operating system built with FreeBSD. Its mission is to deliver a simple, stable, and accessible desktop experience for users who want FreeBSD’s power without the complexity of manual set … ⌘ Read more
Writing Pentest Reports | TryHackMe Write-Up | FarrosFR
Non-members are welcome to access the full story here. Write-Up by FarrosFR | Cybersecurity
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/writing-pentest-reports-tryhackme-wri … ⌘ Read more
I Broke Rate Limits and Accessed 1000+ User Records — Responsibly
👉Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/i-broke-rate-limits-and-accessed-1000-user-records-responsibly-8c45f … ⌘ Read more
How I Gained Root Access on a Vulnerable Web Server: From Reconnaissance to Privilege Escalation
Web Server Exploitation & Privilege Escalation - Full Walkthr … ⌘ Read more
M0SS-101 Synth with BL616 RISC-V Delivers Classic Controls in a Compact DIY Kit
The M0SS-101 is a compact virtual analog monosynth designed for hands-on subtractive synthesis. It features 42 editable parameters accessible through 26 buttons and a rotary encoder, with RGB LEDs providing visual feedback for signal flow and modulation. The synth includes dual oscillators, a multi-mode filter, envelope and LFO control, delay effects, and 17 preset slots […] ⌘ Read more
Accessibility on Linux sucks, but GNOME and KDE are making progress
Accessibility in the software world is a problem in general, but it’s an even bigger problem on open source desktops, as painfully highlighted by this excellent article detailing the utterly broken state of accessibility on Linux. Reading the article is soul-crushing as it starts to dawn on you just how bad the situation really is for those among us who require accessibility features, making it vir … ⌘ Read more
Touch Bar Not Working After MacOS Update? Troubleshooting Black Touch Bar on MacBook Pro
A fair number of MacBook Pro users with Touch Bar equipped Macs have discovered the Touch Bar stops working or goes black after installing a MacOS update. Given that the Touch Bar serves as Function keys, F1, F2, F3 etc keys, as well as toggles for adjusting brightness, system audio, and accessing many MacOS and … Read More ⌘ Read more
Our pledge to help improve the accessibility of open source software at scale
GitHub takes the Global Accessibility Awareness Day (GAAD) pledge.
The post Our pledge to help improve the accessibility of open source software at scale appeared first on The GitHub Blog. ⌘ Read more
1 RPM. This is a rather aggressive rate limit actually. This basically makes Github inaccessible and useless for basically anything unless you're logged in. You can basically kiss "pursuing" casually, anonymously goodbye.
@prologic@twtxt.net that will not be a problem; as long as it doesn’t affect authenticated users it wouldn’t make a difference. But we are comparing apples and eggs here. I don’t access GitHub while unauthenticated, but I can see how others might. It comes across as anti-web in general.
@movq@www.uninformativ.de, “60 requests per hour”, eh? Was that a thing (that is, unauthenticated access to GitHub)?! I know I am on the minority, perhaps, as I rarely (or never) access GitHub unauthenticated.
Bug Chain: pre-auth takeover to permanent access. ⌘ Read more
SSRF via PDF Generator? Yes, and It Led to EC2 Metadata Access
👨💻Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/ssrf-via-pdf-generator-yes-and-it-led-to-ec2-metadata-access-39b8e5b41840 … ⌘ Read more
API Key Exposure in NASA GitHub Repository Leads to Unauthorized Access to Academic Data
🔓Free Article Link
[Continue reading on InfoSec Write-ups »](https://infosecwriteu … ⌘ Read more
Raspberry Pi Connect Exits Beta with Version 2.5 Release
Raspberry Pi has officially ended the beta phase of Raspberry Pi Connect, its remote access platform for connecting to Raspberry Pi devices from anywhere. With the release of version 2.5, the service now includes major updates to connection management, significantly reducing data usage and improving responsiveness. Launched in early 2024, Raspberry Pi Connect quickly gained […] ⌘ Read more
SiFive and Kinara Partner to Launch USB-Based X280 RISC-V Vector Development Board
SiFive and Kinara have announced a new partnership to offer developers direct access to the SiFive Intelligence X280 RISC-V vector processor through a compact USB-based enablement board. The HiFive Xara X280 board, based on Kinara’s Ara-2 processor, is designed to allow early-stage evaluation and development of RISC-V vector software, particularly for AI and machine learning […\ … ⌘ Read more
Design system annotations, part 2: Advanced methods of annotating components
How to build custom annotations for your design system components or use Figma’s Code Connect to help capture important accessibility details before development.
The post [Design system annotations, part 2: Advanced methods of annotating components](https://github.blog/engineering/user-experience/design-system-annotations-part-2-advanced-methods-of-annotating-component … ⌘ Read more
Design system annotations, part 1: How accessibility gets left out of components
The Accessibility Design team created a set of annotations to bridge the gaps that design systems alone can’t fix and proactively addresses accessibility issues within Primer components.
The post [Design system annotations, part 1: How accessibility gets left out of components](https://github.blog/engineering/user-experience/design-system-annotations-part-1-how … ⌘ Read more
UUIDs: A False Sense Of Security
Hi Hunters, would you like to learn about a broken access control vulnerability that I discovered recently for a client.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/uuids-a-false-sense-of-security-10467497daae?source=rss—-7b7 … ⌘ Read more
$50,000 Bounty: GitHub Access Token
How a hidden token in a desktop app could have compromised one of the world’s biggest e-commerce platforms
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/50-000-bounty-github-access-token-c29cb6f00182?source=rss—-7b722bf … ⌘ Read more
HydraLink Offers Open USB-to-Automotive Ethernet Interface for Testing and Diagnostics
HydraLink is now available on CrowdSupply as a compact and open-source USB-to-Automotive Ethernet adapter intended for engineers, researchers, and others working with in-vehicle networks. It supports both 100BASE-T1 and 1000BASE-T1 over single-pair Ethernet, enabling direct access to automotive Ethernet without the need for media converters or additional lab equipment. Hy … ⌘ Read more
**IDOR Attacks Made Simple: How Hackers Access Unauthorized Data **
IDOR Attacks Made Simple: How Hackers Access Unauthorized Data 🔐
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/idor-attacks-made-simple-h … ⌘ Read more
How i Access The Deleted Files of Someone in Google Drive | Bug Bounty ⌘ Read more
**Path Traversal Attack: How I Accessed Admin Secrets **
Path Traversal Attack: How I Accessed Admin Secrets 📂
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/path-traversal-attack-how-i-accessed-admin-secrets-fa5de1865031?source … ⌘ Read more
Unrestricted Access to All User Information | REST API Oversharing ⌘ Read more
Steam to highlight accessibility support for games on store pages
The Steam store and desktop client will soon be able to help players find games that feature accessibility support. If your game has accessibility features, you can now enter that information in the Steamworks ‘edit store’ section for your app. ↫ Steam announcements page I have a lot of criticism for the Steam client application – it’s a overly complex, unattractive, buggy, slow, top-heavy Chrome engi … ⌘ Read more
Prepare your application landscape for zero trust with Keycloak 26.2
Strong identity and access management is a key component of a zero trust architecture for cloud native applications. Keycloak is well-known for its single-sign-on capabilities based on open standards. It provides you all the building blocks… ⌘ Read more
**404 to 0wnage: How a Broken Link Led Me to Admin Panel Access **
Hey there!😁
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/404-to-0wnage-how-a-broken-link-led-me-to-admin-panel-access-2b58e1fffaa3?source=r … ⌘ Read more
** HTTP Parameter Pollution: The Dirty Little Secret That Gave Me Full Backend Access ️**
Free Link🎈
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.co … ⌘ Read more
good morning friends. i don’t know what i’m gonna do today. perhaps work on my patreon and login wall more personal sites behind authelia that i could offer access to via patreon tier
is it like… ethical to offer access to certain self hosted services as patreon exclusives. like i wanna offer the IRC client/bouncer i hosted which seems ok i think because i’ve seen pico.sh offer their instances of that as paid services. but the other ones i have in mind are alt web frontends for stuff like imgur and pinterest. and i just feel weird about it for some reason. idk i’m trying to think of ways to support my server stuff but every time i come up with something it feels weird
Banana Pi BPI-RV2 Gateway Board Integrates Siflower SF21H8898 RISC-V SoC
Banana Pi has introduced the BPI-RV2, an open-source gateway platform developed in collaboration with Siflower. The board is based on the SF21H8898 SoC, a quad-core RISC-V processor designed for industrial and enterprise networking applications such as routers, access points, and control gateways. The Siflower SF21H8898 is built using TSMC’s 12nm FFC process and integrates a […] ⌘ Read more
ActiveX disabled by default in Microsoft 365
ActiveX is a powerful technology that enables rich interactions within Microsoft 365 applications, but its deep access to system resources also increases security risks. Starting this month, the Windows versions of Microsoft Word, Microsoft Excel, Microsoft PowerPoint, and Microsoft Visio will have a new default configuration for ActiveX controls: Disable all controls without notification. ↫ Zaeem Patel at the Microsoft 365 Insider Blog Be ho … ⌘ Read more
