XMPP Providers: projectsegfau.lt
Available since
Feb 7, 2023
·
Website: EN
Service
Cost: Free of charge
Legal notice:
2
persons
Organization:
Private person
Server
Server / Data
locations:
🇮🇳
|
🇨🇭
Professional hosting
Server software: ejab … ⌘ Read more
WWDC 2024 Set for June 10-14, Expect iOS 18, macOS 15, visionOS 2, etc
Apple has announced their annual developer conference, WWDC, will take place from June 10 to June 14 of this year. The majority of WWDC 2024 will be online, however there will be an in-person event and keynote speech on June 10, at Apple’s Cupertino California headquarters. Apple typically unveils new versions of upcoming system software … [Read More](https://osxdaily.com/2024/03/26/wwdc-2024-set- … ⌘ Read more
How Secure are Personal Hotspot Connections from iPhone?
The Personal Hotspot feature on iPhone turns your iPhone cellular connection into a wi-fi hotspot that other nearby devices and computers can use to access the internet. It’s one of those really great features available for iPhone that allows you to work from just about anywhere that you have a cellular connection, and can also … [Read More](https://osxdaily.com/2024/03/23/how-secure-are-personal-hotspot-connections-from- … ⌘ Read more
Extended content warning
I realized recently that I wrote some cringe (to put it mildly) posts in my late adolescent phase. On the one hand, I would of course like to banish these posts from my blog, after all, my opinion has changed completely in some cases since then. But on the other hand, it would be a shame to let this part of my personal development simply disappear. ⌘ Read more
What should I do with my new domain?
I recently complained about domain registrars. But I also recently registered a new domain: j7s.me. A numeronym of my first name. And the .me TLD to show that I am a person. (And it is a short domain that was available.) ⌘ Read more
anthony.buc.ci account. I am assuming these kind of bugs were never addressed by @prologic. :-(
@quark@ferengi.one @mckinley@twtxt.net
i think you have to be following the person so it does it correctly.
** Valentines, patron saint of bees, plague, and sushi **
Hot on the heals of recently being interviewed by Manu, I was interviewed by Kristen Foster-Marks from the Developer Success Lab. It was a lot of fun! We had a wide ranging conversation, but often came back around to the importance of“learning … ⌘ Read more
Enjoy 2 Beautiful Starfield Wallpapers for iPhone, iPad, Mac, from BasicAppleGuy
Using custom wallpapers are one of the simpler but more fun ways you can customize the appearance of your iPhone, iPad, or Mac, and some of my personal favorite wallpapers are space-themed. I recently came across two really beautiful and simple space themed wallpapers from BasicAppleGuy, and I wanted to share them with our audience … [Read More](https://osxdaily.com/2024/02/11 … ⌘ Read more
@movq@www.uninformativ.de the location is real. A few in the ‘hood mentioned seeing this person directly. They live somewhere on the hillside in the background of the video.
Well crap. I think I just realized that if my profile photo was a person it could vote in this year’s election. Probably time for a new default one.
Macintosh Turns 40
The Macintosh computer, which has played a pivotal role in shaping personal computing and design principles throughout the entire tech industry, has turned 40 years old. The first Macintosh debuted on January 23, 1984 as a groundbreaking product. Distinguished with friendly unique hardware design, a revolutionary graphical user interface, the ability to speak text aloud, … Read More ⌘ Read more
Fix Step Count in Health App Updating Slowly on iPhone
If you’re the type of person who likes to keep track of their daily step count by using iPhone as a step counter, it is frustrating when the iPhone Health app step counter does not update as frequently as you’d like. Additionally, there are some challenges that are linked to specific step counts, and many … Read More ⌘ Read more
Low Profile Radxa X2L SBC Featuring Intel J4125 and RP2040 Microcontroller
The Radxa X2L, powered by the Intel Celeron Processor J4125, is a compact yet robust mini-computer designed to cater to a wide range of computing needs. It’s a perfect blend of performance, connectivity, and versatility, making it suitable for both personal and professional use. Unlike other recent Radxa offerings such as the Radxa Zero 3E, […] ⌘ Read more
The XMPP Standards Foundation: XMPP Summit 26
The XMPP Standards Foundation (XSF) will hold its 26th XMPP Summit in Brussels, Belgium this year again!
These are the two days preceding FOSDEM 2024.
The XSF invites everyone interested in development of the XMPP protocol to attend, and discuss all things XMPP in person and remote!
The venue will take place at the Thon Hotel EU including coffee break (from 08:30 o’clock) and lunch (12:00 to 14:00 o’clock) paid b … ⌘ Read more
The XMPP Standards Foundation: XMPP at FOSDEM 2024
We’re very excited to be back at FOSDEM in person in 2024.
Once again, many members of the XSF and the XMPP community will be attending, and we hope to see you there!
As usual, we will host the Realtime Lounge, where you can come and meet community members, project developers, see demos and ask us questions.
We’ll be in our traditional location - find us on the K building 2nd floor, [beside the elevator](https://fosdem.o … ⌘ Read more
** New year **
The last weeks of 2023 have been very enjoyable. Other than having to deal with a cascade of car issues, there’s been a lot of time to hang out with the partner and kids, wander around outside, and poke at fun personal projects…and I mean, work, too, but…you know.
The other evening I pulled together a fun Markov chain toy. It isn’t anything fancy, but I wanted the ability to feed a madlib style script to the program and have it use that as a template to fill in. The resulting program is beak and … ⌘ Read more
Deals: AirTags 4-pack for $80, M2 MacBook Air 15″ for $1049
Amazon continues to offer excellent deals on Apple products, with some great discounts on the MacBook Air 15″ model, AirTags, and more. AirTags for $24, 4-pack for $80 AirTag personal trackers are rarely discounted, but right now they’re $24 each on Amazon, and $80 for a 4-pack: AirTag – single tracker – $24 (down from … [Read More](https://osxdaily.com/2023/12/27/deals-airtags-4-pack-for-80-m2-macbook-air-15-for- … ⌘ Read more
** an approximately programmer-shaped person **
I was recently interviewed by Manu for his People and Blogs series! It was a great honor to be suggested by Piper for that, and I had a blast responding to all of Manu’s questions.
The December Adventure is in full swing. There are so many fun adventure logs this year. I’ve been mostly focusing on building toys with [Decker](https://beyondloom.com/ … ⌘ Read more
Det er nu jeg er *virkelig* glad for at jeg ikke taler et sprog der uregelmæssigt bøjer udsangsord efter et subjekts binære køn.
Gad vide hvordan franskmænd (personer fra frankrig?) takler dén. ⌘ Read more
A type of assumption that really grinds my gears: when someone expects a certain event will happen, and other people immediately assume that means the person wants the event to happen. Thinking something will happen and wanting it to happen are two very different things.
Wondering how that person in Nebraska is doing keeping that cornerstone open-source package going.
How to Make a Contact Poster on iPhone
Contact Posters are a feature added to iPhone with iOS 17 and newer, that allow you to choose a custom photo, poster, and name that appears when you call another iPhone user (or send them a message). These personalized Contact Posters can be a fun way to further customize your iPhone experience, and they’re unique … Read More ⌘ Read more
Anyone else keeping personal .log files updated through basic shell commands?
I acquired a new, fancy domain for a new side project. A site with tips on how to save money on purchases is something I would like to start. The search for a CMS reminds me of why I built GoBlog: all available options are not optimal. But GoBlog also isn’t optimal for this project for various reasons, as it shouldn’t be a typical personal blog. And now I have this really cool domain and question my plans. 😅 ⌘ Read more
Get a Personal Update from Siri on iPhone, iPad, Mac
Siri has a neat largely unknown feature called Personal Update, that, when requested, will give you a summary of information from various apps that you may find useful. Specifically, Personal Update will give you the weather forecast for the day, whatever your calendar events that day are, your reminders, an travel time estimate to locations … [Read More](https://osxdaily.com/2023/10/11/get-a-personal-update-from-siri-on-iphone-ip … ⌘ Read more
Prompting GitHub Copilot Chat to become your personal AI assistant for accessibility
GitHub Copilot Chat can help you learn about accessibility and improve the accessibility of your code. In this blog, we share a sample foundational prompt that instructs GitHub Copilot Chat to become your personal AI assistant for accessibility.
The post [Prompting GitHub Copilot Chat to become your personal AI assistant for accessibility](https://github.blog/2023-10- … ⌘ Read more
Announcing Docker AI/ML Hackathon
With the return of DockerCon, held October 4-5 in Los Angeles, we’re excited to announce the kick-off of a Docker AI/ML Hackathon. Join us at DockerCon — in-person or virtually — to learn about the latest Docker product announcements. Then, bring your innovative artificial intelligence (AI) and machine learning (ML) solutions to life in the hackathon for a chance to win cool prizes. ⌘ Read more
A better Postman alternative: Hoppscotch
I used to use Postman for both personal and work projects. It was great for making HTTP requests without having to create curl commands. But now, Postman requires a login, which I hate. I don’t understand why a login is needed for such a simple tool. ⌘ Read more
Let’s DockerCon!
DockerCon 2023 will be hybrid — both live (in Los Angeles, California) and virtual. Our desire is to once again experience the live magic of the hallway track, the serendipitous developer-to-developer sharing of tips and tricks, and the celebration of our community’s accomplishments … all while looking forward together toward a really exciting future. And for members of our community who can’t attend in person, we hope you’ll join us virtually! ⌘ Read more
More data contradicting the existence of “echo chambers”. As I’ve argued many times before, the concept of an echo chamber or information bubble is not real. The podcast below is an interview of an author of a study where they actually intervened and changed the information diet of 20,000 people (with consent!), then surveyed them after three months. They observed essentially no changes to the study subjects’ beliefs and attitudes. They also observed that the typical person, while they tend to gravitate towards people with similar political leanings, only get about 50% of their content from such like-minded people. They get the rest from neutral sources and maybe 20% from non-like-minded people.
Varied information diet + No change in attitudes when information diet is forced to be different = no echo chamber.
Changes to How Docker Handles Personal Authentication Tokens
Docker is improving the visibility of Docker Desktop and Hub users’ personal access tokens. Specifically, we are changing how tokens are handled across sessions between the two tools. Learn more about this security improvement. ⌘ Read more
@prologic@twtxt.net thank you! Yup, a full half century. Quite weird feeling. I feel like I’ve finally earned my curmudgeonly personality 😆
Det ærger mig også lidt, hvor ofte danskere snakker om USAiansk politik i hverdagen.
Hypotese:
jeg kender flere personer som har holdninger til de seneste 3 af USAs præsidenters politik, end jeg kender personer som kan nævne navnet på den siddende tyske kansler.
Passer det også i jeres vennekredse? Eller er bare det min omgangskreds som er ualmindeligt USA-fokuseret? ⌘ Read more
Hardening repositories against credential theft
Some best practices and important defenses to prevent common attacks against GitHub Actions that are enabled by stolen personal access tokens, compromised accounts, or compromised GitHub sessions.
The post Hardening repositories against credential theft appeared first on The GitHub Blog. ⌘ Read more
@prologic@twtxt.net I had a feeling my container was not running remotely. It was too crisp.
podman is definitely capable of it. I’ve never used those features though so I’d have to play around with it awhile to understand how it works and then maybe I’d have a better idea of whether it’s possible to get it to work with cas.run.
There’s a podman-specific way of allowing remote container execution that wouldn’t be too hard to support alongside docker if you wanted to go that route. Personally I don’t use docker–too fat, too corporate. podman is lightweight and does virtually everything I’d want to use docker to do.
@movq@www.uninformativ.de @mckinley@twtxt.net I believe the resurgence in availability of municipal WiFi is largely driven by the surveillance capabilities it offers. Every person who has WiFi enabled on their phone can be tracked throughout the city as their phones ping various base stations; a lot of folks aren’t aware of just how much information can be slurped out of a phone that isn’t locked down just from its WiFi pings. I know this happens in Toronto, and I was familiar with a startup in Massachusetts that based its business model on this very concept. I can only assume it’s widespread in the US if not throughout the Western world.
snac/the fediverse for a few days and already I've had to mute somebody. I know I come on strongly with my opinions sometimes and some people don't like that, but this person had already started going ad hominem (in my reading of it), and was using what felt to me like sketchy tactics to distract from the point I was trying to make and to shut down conversation. They were doing similar things to other people in the thread so rather than wait for it to get bad for me I just muted them. People get so weirdly defensive so fast when you disagree with something they said online. Not sure I fully understand that.
@prologic@twtxt.net Well, you can mute or block individual users, and you can mute conversations too. I think the tools for controlling your interactions aren’t so bad (they could definitely be improved ofc). And in my case, I was replying to something this person said, so it wasn’t outrageous for his reply to be pushed to me. Mostly, I was sad to see how quickly the conversation went bad. I thought I was offering something relatively uncontroversial, and actually I was just agreeing with and amplifying something another person had already said.
snac/the fediverse for a few days and already I've had to mute somebody. I know I come on strongly with my opinions sometimes and some people don't like that, but this person had already started going ad hominem (in my reading of it), and was using what felt to me like sketchy tactics to distract from the point I was trying to make and to shut down conversation. They were doing similar things to other people in the thread so rather than wait for it to get bad for me I just muted them. People get so weirdly defensive so fast when you disagree with something they said online. Not sure I fully understand that.
@prologic@twtxt.net attacking the person, not the idea. It’d be like if you said “yarn is better than mastodon because it isn’t push based” and someone who disagreed with you said “well you think that because you’re an idiot” or something like that.
I’ve only been using snac/the fediverse for a few days and already I’ve had to mute somebody. I know I come on strongly with my opinions sometimes and some people don’t like that, but this person had already started going ad hominem (in my reading of it), and was using what felt to me like sketchy tactics to distract from the point I was trying to make and to shut down conversation. They were doing similar things to other people in the thread so rather than wait for it to get bad for me I just muted them. People get so weirdly defensive so fast when you disagree with something they said online. Not sure I fully understand that.
Security alert: social engineering campaign targets technology industry employees
GitHub has identified a low-volume social engineering campaign that targets the personal accounts of employees of technology firms. No GitHub or npm systems were compromised in this campaign. We’re publishing this blog post as a warning for our customers to prevent exploitation by this threat actor. ⌘ Read more
An official FBI document dated January 2021, obtained by the American association “Property of People” through the Freedom of Information Act.
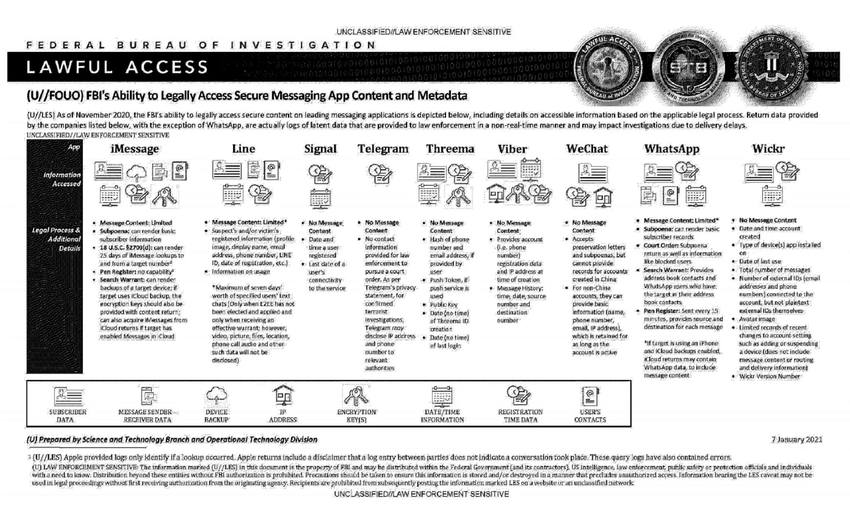
This document summarizes the possibilities for legal access to data from nine instant messaging services: iMessage, Line, Signal, Telegram, Threema, Viber, WeChat, WhatsApp and Wickr. For each software, different judicial methods are explored, such as subpoena, search warrant, active collection of communications metadata (“Pen Register”) or connection data retention law (“18 USC§2703”). Here, in essence, is the information the FBI says it can retrieve:
Apple iMessage: basic subscriber data; in the case of an iPhone user, investigators may be able to get their hands on message content if the user uses iCloud to synchronize iMessage messages or to back up data on their phone.
Line: account data (image, username, e-mail address, phone number, Line ID, creation date, usage data, etc.); if the user has not activated end-to-end encryption, investigators can retrieve the texts of exchanges over a seven-day period, but not other data (audio, video, images, location).
Signal: date and time of account creation and date of last connection.
Telegram: IP address and phone number for investigations into confirmed terrorists, otherwise nothing.
Threema: cryptographic fingerprint of phone number and e-mail address, push service tokens if used, public key, account creation date, last connection date.
Viber: account data and IP address used to create the account; investigators can also access message history (date, time, source, destination).
WeChat: basic data such as name, phone number, e-mail and IP address, but only for non-Chinese users.
WhatsApp: the targeted person’s basic data, address book and contacts who have the targeted person in their address book; it is possible to collect message metadata in real time (“Pen Register”); message content can be retrieved via iCloud backups.
Wickr: Date and time of account creation, types of terminal on which the application is installed, date of last connection, number of messages exchanged, external identifiers associated with the account (e-mail addresses, telephone numbers), avatar image, data linked to adding or deleting.
TL;DR Signal is the messaging system that provides the least information to investigators.
Personally? I’d rather a woman owned Jordan Peterson and got him to shut the fuck up.
I don’t really like the term “gatekeeping”, especially when it’s used to describe the general concept of a barrier to entry. The term “gatekeeping” implies to me a “gatekeeper”–a person A who is trying to control if person B can interact with person C. It implies active discrimination, perhaps even bigotry, when in reality the barrier might be a passive issue such as scarcity or inherent complexity. “Gatekeeping” seems an intentionally- and needlessly-charged term.
Let’s assume for a moment that an answer to a question would be met with so many words you don’t know what the answer was at all. Why? Why do this? Is this a stereotype of academics and philosophers? If so, it’s not a very straight-forward way of thinking, let alone answering a simple question.
Well, I can’t know what’s in these peoples’ minds and hearts. Personally I think it’s a way of dissembling, of sowing doubt, and of maintaining plausible deniability. The strategy is to persuade as many people as possible to change their minds, and then force the remaining people to accept the idea because they think too many other people believe it.
Let’s say you want, for whatever reason, to get a lot of people to accept an idea that you know most people find horrible. The last thing you should do is express the idea clearly and concisely and repeat it over and over again. All you’d accomplish is to cement people’s resistance to you, and label yourself as a person who harbors horrible ideas that they don’t like. So you can’t do that.
What do you do instead? The entire field of “rhetoric”, dating back at least to Plato and Aristotle (400 years BC), is all about this. How to persuade people to accept your idea, even when they resist it. There are way too many techniques to summarize in a twt, but it seems almost obvious that you have to use more words and to use misleading or at least embellished or warped descriptions of things, because that’s the opposite of clearly and concisely expressing yourself, which would directly lead to people rejecting your idea.
That’s how I think of it anyway.
<person> noget andet
BlueSky is cosplaying decentralization
I say “ostensibly decentralized”, because BlueSky’s (henceforth referred to as “BS” here) decentralization is a similar kind of decentralization as with cryptocurrencies: sure, you can run your own node (in BS case: “personal data servers”), but that does not give you basically any meaningful agency in the system.
I don’t know why anyone would want to use this crap. It’s the same old same old and it’ll end up the same old way.
GitHub Copilot X: The AI-powered developer experience
GitHub Copilot is evolving to bring chat and voice interfaces, support pull requests, answer questions on docs, and adopt OpenAI’s GPT-4 for a more personalized developer experience. ⌘ Read more
Erlang Solutions: Presentamos el soporte de transmisión en RabbitMQ
¿Quiere saber más sobre el soporte de transmisión en RabbitMQ? Arnaud Cogoluègnes, ingeniero de personal de VMware, desglosa todo lo que hay que saber en la Cumbre RabbitMQ de 2021.
En julio de 2021, se introdujeron streams a RabbitMQ, utilizando un nuevo protocolo extremadamente rápido que se puede utilizar junto con AMQP 0.9.1. Los [streams](https://www.erlang-solutions.com/blog/rabbitmq-quorum-queues-explaine … ⌘ Read more
This time I’m doing my commute (to my second flat) with this new 70L travel backpack from Decathlon. It’s already full with just my work stuff (notebook, keyboard, mouse) and some other stuff (personal notebook, smaller backpack, toiletries, 2L water bottle). How am I supposed to fit 14 days of vacation stuff in there? 🤔 Good that I can take a vacation without having to take the work stuff with me. 😅 ⌘ Read more
** Ideas for making accessibility and equity a core part of the software development lifecycle **
In accessibility and the product person I said
we need to make accessibility a core part of our processes
Here, I want to talk about that in more detail. I want to briefly explore what making accessibility a part of core processes looks like, and how that is different from centering access … ⌘ Read more