Hey @itsericwoodward@itsericwoodward.com, I just wanna let you know that twtstrm/0.4.0 sends a broken User-Agent header. Instead of the URL, the nick is repeated.
@bender@twtxt.net Thanks for asking!
So, I’ve been working on 2 main twtxt-related projects.
The first is small Node / express application that serves up a twtxt file while allowing its owner to add twts to it (or edit it outright), and I’ve been testing it on my site since the night I made that post. It’s still very much an MVP, and I’ve been intermittently adding features, improving security, and streamlining the code, with an eye to release it after I get an MVP done of project #2 (the reader).
But that’s where I’ve been struggling. The idea seems simple enough - another Node / express app (this one with a Vite-powered front-end) that reads a public twtxt file, parses the “follow” list, grabs (and parses) those twtxt files, and then creates a river of twts out of the result. The pieces work fine in seclusion (and with dummy data), but I keep running into weird issues when reading real-live twtxt files, so some twts come through, while others get lost in the ether. I’ll figure it out eventually, but for now, I’ve been spending far more time than I anticipated just trying to get it to work end-to-end.
On top of it, the 2 projects wound up turning into 4 (so far), as I’ve been spinning out little libraries to use across both apps (like https://jsr.io/@itsericwoodward/fluent-dom-esm, and a forthcoming twtxt helper library).
In the end, I’m hoping to have project 1 (the editor) into beta by the end of October, and project 2 (the reader) into beta sometime after that, but we’ll see.
I hope this has satisfied your curiosity, but if you’d like to know more, please reach out!
MCP Horror Stories: The Drive-By Localhost Breach
This is Part 4 of our MCP Horror Stories series, where we examine real-world security incidents that expose the devastating vulnerabilities in AI infrastructure and demonstrate how Docker MCP Gateway provides enterprise-grade protection against sophisticated attack vectors. The Model Context Protocol (MCP) has transformed how developers integrate AI agents with their development environments. Tools like… ⌘ Read more
@prologic@twtxt.net I know we won’t ever convince each other of the other’s favorite addressing scheme. :-D But I wanna address (haha) your concerns:
I don’t see any difference between the two schemes regarding link rot and migration. If the URL changes, both approaches are equally terrible as the feed URL is part of the hashed value and reference of some sort in the location-based scheme. It doesn’t matter.
The same is true for duplication and forks. Even today, the “cannonical URL” has to be chosen to build the hash. That’s exactly the same with location-based addressing. Why would a mirror only duplicate stuff with location- but not content-based addressing? I really fail to see that. Also, who is using mirrors or relays anyway? I don’t know of any such software to be honest.
If there is a spam feed, I just unfollow it. Done. Not a concern for me at all. Not the slightest bit. And the byte verification is THE source of all broken threads when the conversation start is edited. Yes, this can be viewed as a feature, but how many times was it actually a feature and not more behaving as an anti-feature in terms of user experience?
I don’t get your argument. If the feed in question is offline, one can simply look in local caches and see if there is a message at that particular time, just like looking up a hash. Where’s the difference? Except that the lookup key is longer or compound or whatever depending on the cache format.
Even a new hashing algorithm requires work on clients etc. It’s not that you get some backwards-compatibility for free. It just cannot be backwards-compatible in my opinion, no matter which approach we take. That’s why I believe some magic time for the switch causes the least amount of trouble. You leave the old world untouched and working.
If these are general concerns, I’m completely with you. But I don’t think that they only apply to location-based addressing. That’s how I interpreted your message. I could be wrong. Happy to read your explanations. :-)
ProcessOne: Why Europe’s ‘Chat Control’ Proposal Will Cripple European Communication Industry While Failing to Protect Children
On October 14th, the European Concil will vote on a regulation that … ⌘ Read more
Silent Component Updates & Redesigned Update Experience
Following on from our previous initiative to improve how Docker Desktop delivers updates, we are excited to announce another major improvement to how Docker Desktop keeps your development tools up to date. Starting with Docker Desktop 4.46, we’re introducing automatic component updates and a completely redesigned update experience that puts your productivity first. Why We’re… ⌘ Read more
ProcessOne: Spotify’s Direct Messaging Gambit
Last week, Spotify quietly launched direct messaging across its platform in selected areas, allowing users to share tracks and playlists through private conversations within the app. The feature was rolled out with mini … ⌘ Read more
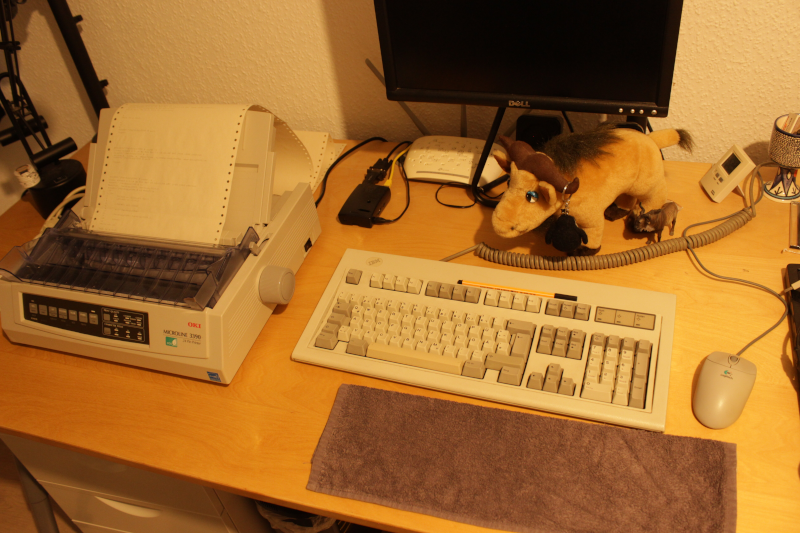
I’ve got a prototype of my hardcopy simulator going. I’m typing on the keyboard and the “display” goes to the printer:
https://movq.de/v/235c1eabac/MVI_8810.MOV.mp4
The biiiiiiiiiig problem is that the print head and plastic cover make it impossible to see what’s currently being printed, because this is not a typewriter. This means: In order to see what I just entered, I have to feed the paper back and forth and back and forth … it’s not ideal.
I got that idea of moving back/forth from Drew DeVault, who – as it turned out – did something similar a few years back. (I tried hard to read as little as possible of his blog post, because figuring things out myself is more fun. But that could mean I missed a great idea here or there.)
But hey, at least this is running on my Pentium 133 on SuSE Linux 6.4, printer connected with a parallel cable. 😍
(Also, yes, you can see the printouts of earlier tests and, yes, I used ed(1) wrong at one point. 🤪 And ls insisted on using colors …)
Here’s an interesting thought/angle on this topic:
gemini://gemini.conman.org/boston/2025/08/21.1
A further check showed that all the network blocks are owned by one organization—Tencent [4]. I’m seriously thinking that the CCP (Chinese Communist Party) encourage this with maybe the hope of externalizing the cost of the Great Firewall [5] to the rest of the world.
The XMPP Standards Foundation: MongooseIM 6.4 - Simplified and Unified
MongooseIM is a scalable and efficient instant messaging server. It implements the open, proven, extensible and constantly evolving XMPP protocol, which is an excellent choice when it comes to instant messaging. To communicate with other XMPP entities, the server uses three main types of interfaces, listed in the table below.
XMPP InterfacePurposeConnection typeReworked in v … ⌘ Read more
Why everyone is quitting social media ⌘ Read more
Erlang Solutions: MongooseIM 6.4: Simplified and Unified
MongooseIM is a scalable and efficient instant messaging server. With the latest release 6.4.0, it has become more powerful yet easier to use and maintain. Thanks to the internal unification of listeners and connection handling, the configuration is easier and more intuitive, while numerous new options are supported.
New features include support for TLS 1.3 with optional channel binding for improved security, single round-trip authent … ⌘ Read more
(Just for fun, SuSE Linux 6.4 from ~25 years ago: 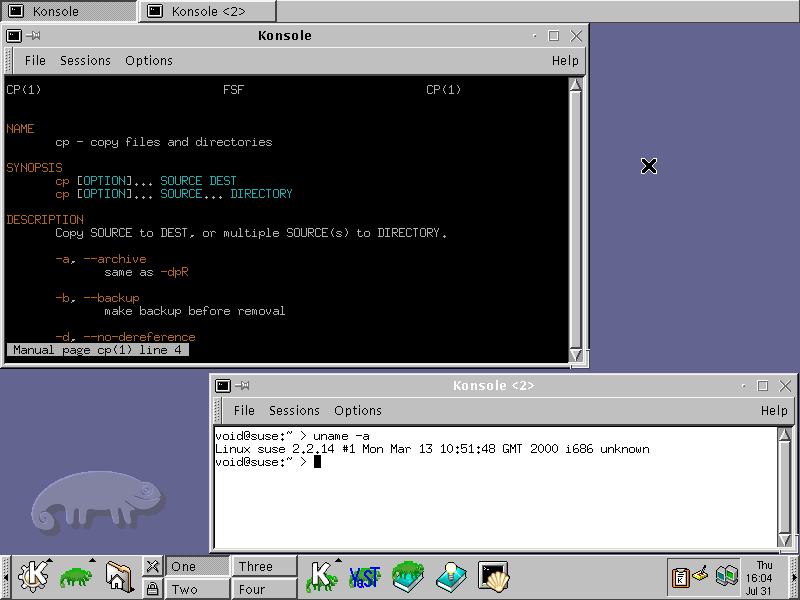 )
)
@lyse@lyse.isobeef.org @kat@yarn.girlonthemoon.xyz Colorized manpages have been a thing for a very long time:
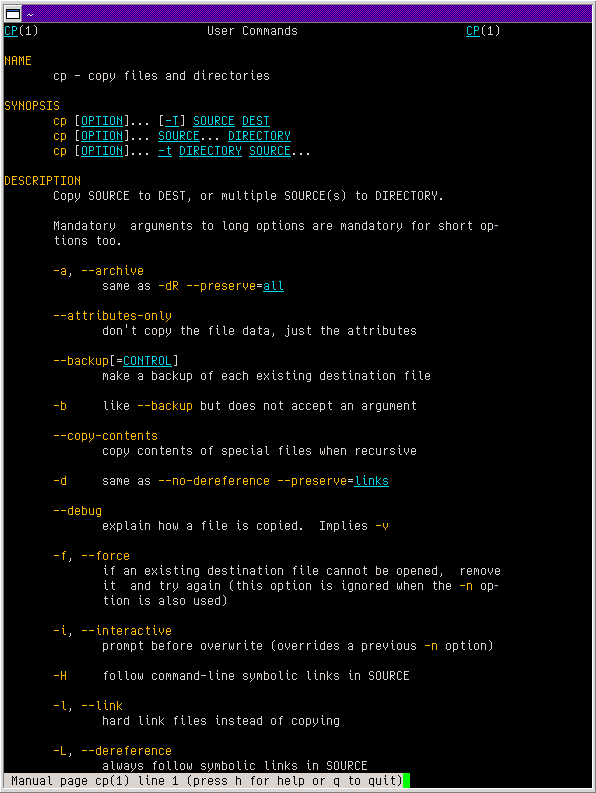
Problem is, hardly anybody knows this, because you configure this by … drumroll … overwriting TERMCAP entries of less in your ~/.bashrc:
export LESS_TERMCAP_md=$'\e[38;5;3m' # Bold
export LESS_TERMCAP_me=$'\e[0m' # End Bold
export LESS_TERMCAP_us=$'\e[4;38;5;6m' # Underline
export LESS_TERMCAP_ue=$'\e[0m' # End Underline
export GROFF_NO_SGR=1 # Needed since groff 1.23
@kat@yarn.girlonthemoon.xyz https://snippets.4-walls.net/kat/890f9db00b1940679161d0348b28c339
@lyse@lyse.isobeef.org 4 years. 🫤
i am having fun with dmenu
https://bytes.4-walls.net/kat/dotfiles/src/branch/main/config/.local/bin/dict
https://bytes.4-walls.net/kat/dotfiles/commit/b5ca2e0eaba3cbc0cf0898926ffcb0bb064d17c7
@kat@yarn.girlonthemoon.xyz NVM i stole other peoples code to make a dictionary lookup script https://bytes.4-walls.net/kat/dotfiles/src/branch/main/config/.local/bin/dict
@lyse@lyse.isobeef.org @kat@yarn.girlonthemoon.xyz I spent so much time in the past figuring out if something is a dict or a list in YAML, for example.
What are the types in this example?
items:
- part_no: A4786
descrip: Water Bucket (Filled)
price: 1.47
quantity: 4
- part_no: E1628
descrip: High Heeled "Ruby" Slippers
size: 8
price: 133.7
quantity: 1
items is a dict containing … a list of two other dicts? Right?
It is quite hard for me to grasp the structure of YAML docs. 😢
The big advantage of YAML (and JSON and TOML) is that it’s much easier to write code for those formats, than it is with XML. json.loads() and you’re done.
The WM_CLASS Property is used on X11 to assign rules to certain windows, e.g. “this is a GIMP window, it should appear on workspace number 16.” It consists of two fields, name and class.
Wayland (or rather, the XDG shell protocol – core Wayland knows nothing about this) only has a single field called app_id.
When you run X11 programs under Wayland, you use XWayland, which is baked into most compositors. Then you have to deal with all three fields.
Some compositors map name to app_id, others map class to app_id, and even others directly expose the original name and class.
Apparently, there is no consensus.
@movq@www.uninformativ.de Yeah, it’s a shitshow. MS overconfirms all my prejudices constantly.
Ignoring e-mail after lunch works great, though. :-)
Our timetracking is offline for over a week because of reasons. The responsible bunglers are falling by the skin of their teeth: ![]()
- The error message neither includes the timeframe nor a link to an announcement article.
- The HTML page needs to download JS in order to display the fucking error message.
- Proper HTTP status codes are clearly only for big losers.
- Despite being down, heaps of resources are still fetched.
I find it really fascinating how one can screw up on so many levels. This is developed inhouse, I’m just so glad that we’re not a software engineering company. Oh wait. How embarrassing.
@prologic@twtxt.net Yeah, this really could use a proper definition or a “manifest”. 😅 Many of these ideas are not very wide spread. And I haven’t come across similar projects in all these years.
Let’s take the farbfeld image format as an example again. I think this captures the “spirit” quite well, because this isn’t even about code.
This is the entire farbfeld spec:
farbfeld is a lossless image format which is easy to parse, pipe and compress. It has the following format:
╔════════╤═════════════════════════════════════════════════════════╗
║ Bytes │ Description ║
╠════════╪═════════════════════════════════════════════════════════╣
║ 8 │ "farbfeld" magic value ║
╟────────┼─────────────────────────────────────────────────────────╢
║ 4 │ 32-Bit BE unsigned integer (width) ║
╟────────┼─────────────────────────────────────────────────────────╢
║ 4 │ 32-Bit BE unsigned integer (height) ║
╟────────┼─────────────────────────────────────────────────────────╢
║ [2222] │ 4x16-Bit BE unsigned integers [RGBA] / pixel, row-major ║
╚════════╧═════════════════════════════════════════════════════════╝
The RGB-data should be sRGB for best interoperability and not alpha-premultiplied.
(Now, I don’t know if your screen reader can work with this. Let me know if it doesn’t.)
I think these are some of the properties worth mentioning:
- The spec is extremely short. You can read this in under a minute and fully understand it. That alone is gold.
- There are no “knobs”: It’s just a single version, it’s not like there’s also an 8-bit color depth version and one for 16-bit and one for extra large images and one that supports layers and so on. This makes it much easier to implement a fully compliant program.
- Despite being so simple, it’s useful. I’ve used it in various programs, like my window manager, my status bars, some toy programs like “tuxeyes” (an Xeyes variant), or Advent of Code.
- The format does not include compression because it doesn’t need to. Just use something like bzip2 to get file sizes similar to PNG.
- It doesn’t cover every use case under the sun, but it does cover the most important ones (imho). They have discussed using something other than RGBA and decided it’s not worth the trouble.
- They refrained from adding extra baggage like metadata. It would have needlessly complicated things.
** Om nom nom LLMs, in which I respond to Simon Willison’s analogy **
I am hesitant to wade into the tumultuous waters that are the discourse around generative AI and LLMs, but this morning I came across a thing that so thoroughly melted my brain I feel uncontrollably compelled to respond.
This morning, at evidently 4:10 AM (no mention of timezone), Simon Willison shared the following blog post, quoted here in full:
Quitting programming as … ⌘ Read more
Saw this on Mastodon:
https://racingbunny.com/@mookie/114718466149264471
18 rules of Software Engineering
- You will regret complexity when on-call
- Stop falling in love with your own code
- Everything is a trade-off. There’s no “best” 3. Every line of code you write is a liability 4. Document your decisions and designs
- Everyone hates code they didn’t write
- Don’t use unnecessary dependencies
- Coding standards prevent arguments
- Write meaningful commit messages
- Don’t ever stop learning new things
- Code reviews spread knowledge
- Always build for maintainability
- Ask for help when you’re stuck
- Fix root causes, not symptoms
- Software is never completed
- Estimates are not promises
- Ship early, iterate often
- Keep. It. Simple.
Solid list, even though 14 is up for debate in my opinion: Software can be completed. You have a use case / problem, you solve that problem, done. Your software is completed now. There might still be bugs and they should be fixed – but this doesn’t “add” to the program. Don’t use “software is never done” as an excuse to keep adding and adding stuff to your code.
@prologic@twtxt.net … or just bullshit.
I’m Alex, COO at ColdIQ. Built a $4.5M ARR business in under 2 years.
Some “C-level” guy telling people what to do, yeah, I have my doubts.
@movq@www.uninformativ.de make that 4 people! i use plain text when i can because this page convinced me lmfao
@movq@www.uninformativ.de Me too 😅 – Speaking of which i know you’ve lost a bit of “mojo” or “energy” (so have i of late), rest assured, I want to keep the status quo here with what we’ve built, keep it simple and change very little. What we’ve built has worked very well for 5+ years and we have at least 3 very strong clients (maybe 4 or 5?).
@movq@www.uninformativ.de Ahh but it kind of is mine 😅 Or at least I’ve done this kind of thing at least 3 or 4 times now 🤣
Ghost in the Network ⌘ Read more
Cracking JWTs: A Bug Bounty Hunting Guide [Part 6] ⌘ Read more
GraphQL Gatecrash: When an Introspection Query Opened the Whole Backend ️
Free Link 🎈
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/graphql-gatecrash-when-an-intro … ⌘ Read more
Practical study material OSWP Part 3: WEP Walkthrough ⌘ Read more
Practical study material OSWP Part 2: WPA2-MGT Walkthrough ⌘ Read more
Practical study material OSWP Part 1: WPA2-PSK Walkthrough ⌘ Read more
Could XSS Be the Hidden Key to Account Takeover
What if I told you that a simple Cross-Site Scripting (XSS) vulnerability could be the golden ticket to a full Account Takeover (ATO)? No…
[Continue reading on InfoSec Write-ups »](https://infosecwriteups … ⌘ Read more
OSWE Web Hacking Tips (IPPSEC): Java Reversing href=”https://we.loveprivacy.club/search?q=%232”>#2** ⌘ Read more
Crafting Standalone Python Proof of Concept Exploits
Creating standalone proof of concept exploits implementing a zero-to-hero method, requiring a single action to run.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/craf … ⌘ Read more
$560 Bounty: How Twitter’s Android App Leaked User Location
A Silent Broadcast That Let Any App Spy on You Without Asking
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/560-bounty-how-twitters-android-app-leaked- … ⌘ Read more
Mexican Police kill 4 gunmen, cross into Guatemala in dramatic border shootout. ⌘ Read more
Illicit tobacco crop worth $4.4m discovered near Shepparton after tip-off
Authorities seize a 20-tonne crop of mature tobacco being grown on 2.4 hectares, an area equivalent to more than 450 tennis courts, in Victoria’s north. ⌘ Read more
50 Command Line Tools You Wish You Knew Sooner
Master the terminal with these essential commands that will transform your Linux experience from novice to power user.
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/50-command-line-tools-you-wis … ⌘ Read more
My Laptop Died, So I Hacked with My Phone. No Excuse ⌘ Read more
ToolHive Tutorial: Securely Deploy and Manage MCP Servers ⌘ Read more
**️ Deloitte Virtual Internship Cyber Sim Victory ** ⌘ Read more
Nintendo Switch 2 Hacked in 48 Hours — But Here’s Why It’s Just the Beginning
A harmless green line on the screen may have just opened the floodgates for hackers — inside the first real exploit on Nintendo’ … ⌘ Read more
When you play the Game of RBAC, You either validate, or the world denies your existence — like a King behind the wall.
OIDC: The Digitally signed Pinky Swear “It’s Me” (Part I)
Whenever an Elbow-Shake Protocol is being established, there’s always Users try to communicate safely during Corona pandemic!
[Continue reading on InfoSec Write-ups »](https://infosecwrit … ⌘ Read more
WebSocket Wizardry: How a Forgotten Channel Let Me Sniff Private Chats in Real-Time ️♂️
Hey there!😁
[Continue reading on InfoSec Write-ups »]( … ⌘ Read more