Base: 1.75 miles, 00:09:42 average pace, 00:16:58 duration
had to stop for code brown.
#running #treadmill
It seems like I finally fixed a memory leak in GoBlog yesterday, that sometimes made my blog crashing. How? I used Anthropic’s new Claude 3.5 Sonnet to write me a new HTTP compression middleware that compresses HTTP responses using zstd or gzip when possible. I needed to instruct a few changes and modify some code lines as the initial implementation was wrong, but thereafter, it finally seems to work better than my original implementation that probably leaked some objects anywhere. Claude also helped me to write uni … ⌘ Read more
ReadMeAI: An AI-powered README Generator for Developers
The ReadMeAI tool allows users to upload a code file and describe their project. The tool generates documentation in Markdown code for immediate preview and editing. ⌘ Read more
Attack of the clones: Getting RCE in Chrome’s renderer with duplicate object properties
In this post, I’ll exploit CVE-2024-3833, an object corruption bug in v8, the Javascript engine of Chrome, that allows remote code execution (RCE) in the renderer sandbox of Chrome by a single visit to a malicious site.
The post [Attack of the clones: Getting RCE in Chrome’s renderer with duplicate object properties](https://github.blog/2024-06-26-attack-of-the-cl … ⌘ Read more
Why you do not want a visualization of your Infrastructure as Code
Originally published on the appCD blog by Asif Awan You’ve been working on a new application for your company. It is going to address business requirements needed to delight customers. But while you are ready to ship your… ⌘ Read more
Execute commands by sending JSON? Learn how unsafe deserialization vulnerabilities work in Ruby projects
Can an attacker execute arbitrary commands on a remote server just by sending JSON? Yes, if the running code contains unsafe deserialization vulnerabilities. But how is that possible? In this blog post, we’ll describe how unsafe deserialization vulnerabilities work and how you can detect them in Ruby projects.
The post [Execute c … ⌘ Read more
@prologic@twtxt.net hey mate, all working well here so far. The login issue isn’t really an issue as far as actually logging in goes, rather if I get my password wrong it gives the response error code in console, the response of which contains the HTML for the wrong password page if you inspect it, but on the frontend itself nothing actually happens which is the confusion. Just stays on the login page as if it was never submitted. Am I alone in having this issue as well?
How we improved push processing on GitHub
Pushing code to GitHub is one of the most fundamental interactions that developers have with GitHub every day. Read how we have significantly improved the ability of our monolith to correctly and fully process pushes from our users.
The post How we improved push processing on GitHub appeared first on The GitHub Blog. ⌘ Read more
Tulip Creative Computer: ESP32-Based Board for Music and Coding Projects
The Tulip Creative Computer is a development platform aimed at enthusiasts of coding, music, and digital arts. Based on the powerful ESP32-S3 chipset, the Tulip features a 7-inch touchscreen with a 1024 x 600 resolution for custom graphical user interfaces. The Tulip Creative Computer is powered by the ESP32-S3 chip, which includes a 32-bit LX7 […] ⌘ Read more
New York Times Source Code Leaked (and verified)
Over 3.6 Million files totaling over 334 GB. And it’s real. Source code. Documentation. Markdown files. The works. ⌘ Read more
Build Your Own AI-Driven Code Analysis Chatbot for Developers with the GenAI Stack
We dive into a winning Docker AI/ML Hackathon submission, Code Explorer, in the hope that it sparks project ideas for you. ⌘ Read more
GitHub and JFrog partner to unify code and binaries for DevSecOps
This partnership between GitHub and JFrog enables developers to manage code and binaries more efficiently on two of the most widely used developer platforms in the world.
The post GitHub and JFrog partner to unify code and binaries for DevSecOps appeared first on The GitHub Blog. ⌘ Read more
Room Code
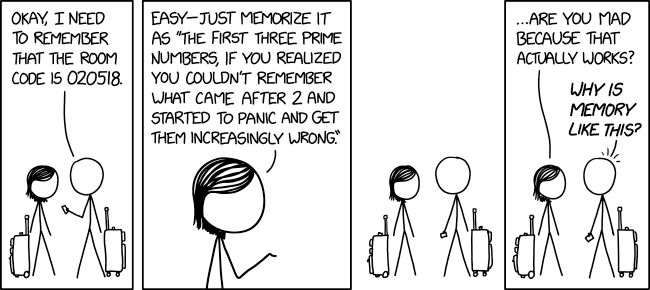 ⌘ Read more
⌘ Read more
Room Code
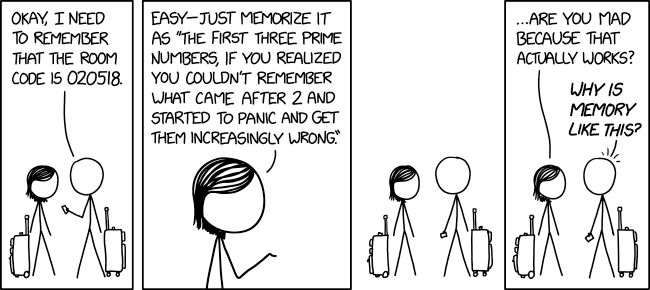 ⌘ Read more
⌘ Read more
Scaling accessibility within GitHub and beyond
GitHub celebrates Global Accessibility Awareness Day by launching another installment of the Coding Accessibility series and sharing how we scale accessibility within GitHub and beyond.
The post Scaling accessibility within GitHub and beyond appeared first on The GitHub Blog. ⌘ Read more
This blog has no Onion Service anymore
I had Tor support in GoBlog for over three years now, but I decided to disable it on my blog (and the GoBlog blog) for now. Several times, Tor randomly started using a lot of memory on my VPS and even crashed my block one or two times. It could have been the Go library used to integrate Tor, or something else in the Tor code itself, I don’t know. ⌘ Read more
How AI enhances static application security testing (SAST)
Here’s how SAST tools combine generative AI with code scanning to help you deliver features faster and keep vulnerabilities out of code.
The post How AI enhances static application security testing (SAST) appeared first on The GitHub Blog. ⌘ Read more
GitHub Copilot Chat in GitHub Mobile is now generally available
With GitHub Copilot Chat in GitHub Mobile, developers can collaborate, ask coding questions, and gain insights into both public and private repositories anywhere, anytime–all in natural language for users on all GitHub Copilot plans.
The post GitHub Copilot Chat in GitHub Mobile is now generally available appeared first on The GitHub Blog. ⌘ Read more
Is your supply chain secure? Double check with our framework
A secure supply chain is a critical piece of cloud native security, and it can be tricky to get right because it covers such a broad expanse of factors from code to pipelines and beyond. Join us on… ⌘ Read more
5 tips to supercharge your developer career in 2024
From mastering prompt engineering to leveraging AI for code security, here’s how you can excel in today’s competitive job market.
The post 5 tips to supercharge your developer career in 2024 appeared first on The GitHub Blog. ⌘ Read more
GitHub Copilot Workspace: Welcome to the Copilot-native developer environment
We’re redefining the developer environment with GitHub Copilot Workspace - where any developer can go from idea, to code, to software all in natural language.
The post GitHub Copilot Workspace: Welcome to the Copilot-native developer environment appeared first on The GitHub Blog. ⌘ Read more
Microsoft Releases DOS 4.0 Source Code… but it Doesn’t Compile!
Listen now (56 mins) | Plus: Source comments, by Microsoft, calling the creator of DOS “brain-damaged” get censored. ⌘ Read more
MS-DOS 4.0 Source Code Fails to Compile
Plus: Source comments, by Microsoft, calling the creator of DOS “brain-damaged” get censored. ⌘ Read more
Erlang Solutions: Technical debt and HR – what do they have in common?
At first glance, it may sound absurd. Here we have technical debt, a purely engineering problem, as technical as it can get, and another area, HR, dealing with psychology and emotions, put into one sentence. Is it possible that they are closely related? Let’s take it apart and see.
What is technical debt, anyway? A tongue-in-cheek definition is that it is code written by someo … ⌘ Read more
What is infrastructure from code?
Member post originally published on AppCD’s blog by Lauren Rother Maybe you’ve heard of Infrastructure as Code (IaC), which is the process of managing and provisioning computer data center resources (mostly but not entirely in the cloud) through version-controlled, machine-readable… ⌘ Read more
Even though the bridges that #beeper use are AGPL licensed, the beeper client is proprietary software 😭
This is big sad.
They almost had it.
It is also kind of limited on google-free android phones, since the QR code scanner for device verification key-signing depends on a google play services API (which microg doesn’t implement). This means that you can’t share message history between your google-free android and the beeper desktop client. ⌘ Read more
Added support for #tag clouds and #search to timeline. Based on code from @dfaria.eu@dfaria.eu🙏
Live at: http://darch.dk/timeline/?profile=https://darch.dk/twtxt.txt
Membership change source code interpretation
Member post originally published on Medium by DatenLord Background In distributed system application scenarios, it is inevitable to add or delete nodes or replace nodes, the simplest solution is to temporarily shut down the cluster, then directly modify… ⌘ Read more
Security research without ever leaving GitHub: From code scanning to CVE via Codespaces and private vulnerability reporting
This blog post is an in-depth walkthrough on how we perform security research leveraging GitHub features, including code scanning, CodeQL, and Codespaces.
The post [Security research without ever leaving GitHub: From code scanning to CVE via Codespaces and private vulnerability reporting](htt … ⌘ Read more
OpenSSH and XZ/liblzma: A nation-state attack was thwarted, what did we learn?
Docker CTO Justin Cormack looks at what we can learn from malicious code in upstream tarballs of xz targeted at subset of OpenSSH servers. “It is hard to overstate how lucky we were here, as there are no tools that will detect this vulnerability.” ⌘ Read more
Telegram Premium allows you to convert voice messages to text. But Telegram Premium isn’t officially available in Germany. So why not develop your own solution? That’s exactly what I did this morning: I created a Telegram bot that takes the voice message and transcribes it using OpenAI’s Whisper API. The bot runs as a serverless container on Scaleway. The source code is published on my Gitea instance. ⌘ Read more
Workflow automation & pipeline portability with AI-driven DevEx
Member post originally published on Ozone’s blog by Amina Reshma What’s the Deal with DevEx? Crack the Code: Ever wondered about developer experience, a.k .a. DevEx? Well, it’s the whole shebang – the vibe, the tools, the rituals –… ⌘ Read more
If AI coding machines become mainstream in less than ten years no human will be able to understand how any digital service works any more.
Even AI coding machines will need to rotate their access credentials every 90 days.
How to use GitHub Copilot in your IDE: tips, tricks, and best practices
GitHub Copilot is a powerful AI assistant. Learn practical strategies to get the most out of GitHub Copilot to generate the most relevant and useful code suggestions in your editor.
The post How to use GitHub Copilot in your IDE: tips, tricks, and best practices appeared first on [The GitHub Bl … ⌘ Read more
Found means fixed: Introducing code scanning autofix, powered by GitHub Copilot and CodeQL
Now in public beta for GitHub Advanced Security customers, code scanning autofix helps developers remediate more than two-thirds of supported alerts with little or no editing.
The post [Found means fixed: Introducing code scanning autofix, powered by GitHub Copilot and CodeQL](https://github.blog/2024-03-20-found-means-fixed-introducing-code-scanning-autofix … ⌘ Read more
Gaining kernel code execution on an MTE-enabled Pixel 8
In this post, I’ll look at CVE-2023-6241, a vulnerability in the Arm Mali GPU that allows a malicious app to gain arbitrary kernel code execution and root on an Android phone. I’ll show how this vulnerability can be exploited even when Memory Tagging Extension (MTE), a powerful mitigation, is enabled on the device.
The post [Gaining kernel code execution on an MTE-enabled Pixel 8](https://github.blog/2024-03-18-gaining-kerne … ⌘ Read more
It not that easy @xuu@txt.sour.is since I implemented webmentions in a different way that how it have been done in yarnd to work with txt-files. You can find the code in webmention_endpoint.php and new_twt.php at main · sorenpeter/timeline
Hard and soft skills for developers coding in the age of AI
While AI revolutionizes software development, it still relies on developers to pilot its use. In this blog, we’ll cover the skills that developers need to have for navigating this new AI-powered coding frontier.
The post Hard and soft skills for developers coding in the age of AI appeared first on [The GitHub Blog](https:// … ⌘ Read more
I wrote up a lab report on my daily to-do tracking “system”, mostly so I could stop thinking about it. The report is at http://a.9srv.net/reports/daily.pdf and the referenced code is at http://txtpunk.com/daily/index.html.
@shreyan@twtxt.net What do you mean when you say federation protocol?
Either use webfinger for identity like mastodon etc. or use ATproto from Bluesky (or both?)
We can use webmentions or create our own twt-mentions for notifying someones feed (WIP code at: https://github.com/sorenpeter/timeline/tree/webmention/views)
I’m not sure we need much else. I would not even bother with encryption since other platforms does that better, and for me twtxt/yarn/timeline is for making things public
How AI code generation works
Explore the capabilities and benefits of AI code generation, and how it can improve the developer experience for your enterprise.
The post How AI code generation works appeared first on The GitHub Blog. ⌘ Read more
Insider newsletter digest: Cook up a controller with GitHub Copilot
Whether you’re coding up a storm or cooking up code, building a controller function with AI is your secret sauce to a flavorful app.
The post Insider newsletter digest: Cook up a controller with GitHub Copilot appeared first on The GitHub Blog. ⌘ Read more
Coding a Web Server in 25 Lines - Computerphile ⌘ Read more
Pinellas County - Tempo: 6.26 miles, 00:08:33 average pace, 00:53:29 duration
whew, it was a tough one. very little sleep from working late last night and an early morning for my son’s coding club. it was a pleasant run, but it really took the energy out of me.
#running
How to Automatically Fill SMS Passcodes & Security Codes on iPhone, iPad, Mac
Messages for iPhone, Mac, and iPad all contain a really handy feature that autofills security codes that are sent to you via text message. You know the type, as these text message verification codes are often required for signing into financial institutions or many other things that use it as a method of identity and … [Read More](https://osxdaily.com/2024/02/20/how-to-automatic … ⌘ Read more
Build code security skills with the GitHub Secure Code Game
Learn to find and fix security issues while having fun with Secure Code Game, now with new challenges focusing on JavaScript, Python, Go, and GitHub Actions!
The post Build code security skills with the GitHub Secure Code Game appeared first on The GitHub Blog. ⌘ Read more
Fixing security vulnerabilities with AI
A peek under the hood of GitHub Advanced Security code scanning autofix.
The post Fixing security vulnerabilities with AI appeared first on The GitHub Blog. ⌘ Read more
How to Autofill Security Codes from Mail on Mac, iPhone, iPad
The latest versions of Mail for iPhone, Mac, and iPad support a fantastic autofill security code feature. This is similar to the autofilling security code feature for SMS that is available in Messages for Mac, iPhone, and iPad, except of course that it’s utilizing the Mail app for two-factor authentication and security codes that are … [Read More](https://osxdaily.com/2024/02/14/how-autofill-security-code-mail-iphone-ipad-ma … ⌘ Read more
“no-code” and “low-code” is still someone else’s code.